For the last week news sources have been full of controversy over the NSA’s controversial PRISM surveillance program (check the latest comments on my Security trends for 2013 article) after top-secret slides detailing the massive electronic surveillance programme were leaked last week by ex-CIA techie Edward Snowden.
If those newspaper reports are accurate, the NSA’s surveillance programs are enormous and sophisticated, and rely on the latest in analytics software. The NSA may have set aside a paltry annual budget of $20m for its internet-data hoovering program. In the face of that, is there any way to keep your communications truly private?
Kenneth Falck comments on his blog the situation around this security like this: Global awareness of PRISM would be good for promoting end-to-end encryption (instead of trusting Skype/Facebook), but I see no activity. ![]()
Slashdot posting Keeping Your Data Private From the NSA (And Everyone Else) seems to promote that idea of using encryption techniques to keep NSA out of your communications. It says that fortunately there are ways to gain a measure of security: HTTPS, Tor, SCP, SFTP, and the vendors who build software on top of those protocols.
The downside is that those host-proof solutions offer security in exchange for some measure of inconvenience. Keeping Your Data Private from the NSA (and Everyone Else) article article give your instructions how you can use HTTPS, Tor, SCP and SFTP to secure your communications. What do you think is the best way to keep your data locked down?
29 Comments
Tomi says:
Ask Slashdot: How To Bypass Gov’t Spying On Cellphones?
http://yro.slashdot.org/story/13/06/13/1632210/ask-slashdot-how-to-bypass-govt-spying-on-cellphones
“It’s doable today to use a mix of virtual machines, VPN, TOR, encryption (and staying away from certain places; like Google Plus, Facebook, and friends), in order to retain a reasonable degree of privacy. In recent days, even major mainstream on-line magazines have published such information.”
“But what about the cell-phone?”
Tomi Engdahl says:
PRISM fears give private search engine DuckDuckGo its best week ever
http://venturebeat.com/2013/06/13/prism-fears-give-private-search-engine-duckduckgo-its-best-week-ever/
If you want to know just how crazy fear over PRISM-like surveillance has made the Internet, take a look at DuckDuckGo.
Thanks to the National Security Agency leaks and some well-timed media appearances, the private search engine is having its best traffic week ever. Visitors to the site made a record 2.35 million direct searches on Wednesday — a 26 percent increase over the previous week.
Tomi says:
Quality Magazines corrective scoops: NSA does not have a direct link with the network data
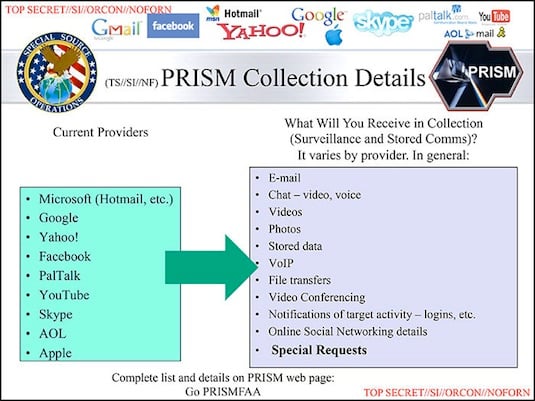
On Thursday night The Washington Post and British newspaper The Guardian simultaneously revealed evidence of a top secret National Security Agency program called PRISM which supplies the federal intelligence agency “direct access” to major Silicon Valley corporations such as Google GOOG -0.26%, Apple AAPL -1.37%, Yahoo YHOO -0.38%, Microsoft, and Skype. The Post and Guardian broke the story after publishing sections of a classified NSA PowerPoint presentation document.
The NSA spying scandal revealed in The Guardian and The Washington Times have corrected the claims. Initially, newspapers reported that the U.S. Internal Security Agency should direct access to Facebook, Microsoft and Google’s servers.
By Friday afternoon many companies had time to issue official comments, all denying knowledge and participation.
Once PRISM became public knowledge outrage and vitriol sprung forth on Twitter, national news outlets jumped into action and picked up the story, and the Director of National Intelligence James Clapper delivered a heavily worded response. On Friday morning the Beltway ground into momentum finally resulting in a televised statement by President Barack Obama while he was paying visit to California.
Only three groups–the federal government, the reporters at The Washington Post and The Guardian, and the leaker–know what the slides say (in so far as only 4 of 41 slides have been released) and how deep a connection the program has to Silicon Valley.
The Washington Post corrected the false information on the British release faster. Both the original magazine story was modified several times, and was on the follow-up stories, which in the end was correctly found that the network giants provide information to the Agency or to NSA direct access to the servers.
Other media and online conversations have been criticized by both the magazine to precipitation. Information spy system was based on leaked documents, including the film set, with the PRISM system was introduced. Portions of a film refers to “direct access to the servers,” which leaves the nature of the system more open to interpretation than a fast one might think.
Sources:
Laatulehdet korjaavat skuuppejaan: NSA:lla ei ole suoraa yhteyttä verkkopalvelujen tietoihin
http://www.tietoviikko.fi/kaikki_uutiset/laatulehdet+korjaavat+skuuppejaan+nsalla+ei+ole+suoraa+yhteytta+verkkopalvelujen+tietoihin/a909447?s=r&wtm=tietoviikko/-15062013&
Fulsome Prism Blues: The Guardian Offers 2nd-Worst Clarification Ever On NSA Story
http://www.mediaite.com/online/fulsome-prism-blues-the-guardian-offers-2nd-worst-clarification-ever-on-nsa-story/
Washington Post Updates, Hedges On Initial PRISM Report
http://www.forbes.com/sites/jonathanhall/2013/06/07/washington-post-updates-hedges-on-initial-prism-report/
Tomi Engdahl says:
Raspberry Pi Tor proxy lets you take anonymity with you
http://hackaday.com/2013/06/15/raspberry-pi-tor-proxy-lets-you-take-anonymity-with-you/
Your web traffic is being logged at many different levels. There are a few different options to re-implement your privacy (living off the grid excluded), and the Tor network has long been one of the best options. But what about when you’re away from you home setup? Adafruit has your back. They’ve posted a guide which will turn a Raspberry Pi into a portable Tor proxy.
A bit of work configuring the Linux network components will turn the RPi into a WiFi access point. Connect to it with your laptop or smartphone and you can browse like normal. The RPi will anonymize the IP address for all web traffic.
Tomi says:
Online there is no safe countries – only one way to protect
Unencrypted files and messages are also at risk in Europe, and the United States only to the services. The only way to protect yourself from surveillance is the encryption of messages.
All kinds of internet traffic is listened to all over the world, so trade secrets or proprietary information should not be sent without any encryption, say 3T’s interviewed by security experts.
Outside your organization outgoing messages must be encrypted if there is anything worthy of protection, advises the Security Service Deputy Director Erka Koivunen Communications Regulatory Authority.
“Risk assessment is to be assumed that the signal intelligence are widely in the world. It is committed by criminals and the authorities. ”
uss viranomaisurkinnasta online services are focused too much on the United States, says the war Doctor Jarno Limnéll.
“Just be sure to at least the biggest ones will do the same as the United States, and this mode of operation is increasing,” says Limnéll, who works cyber security director security company Stonesoft.
Finnish encrypt email very rarely, experts say.
E-mail the protection using PGP encryption method works for a long way.
“If you put your trade secrets or information about the private matters of the cloud, it is advisable to hide from end to end.”
“The only sure way to prevent the information from reaching the U.S. safety authorities should be to avoid the U.S. servers for service providers,” says EK’s corporate security office Jyrki Hollmén.
Hollmén believe in the Finnish operators’ services to be more safe and secure.
“Each company has to decide how to deal with the matter.”
Safety checklist:
1 Drag the border to where and how to store the information.
2 Encrypt files and messages, as the case requires privacy.
3 Avoid foolish perusmokat. Do not pick up guests from the street usb stick.
4 Security requires constant updating.
Source: http://www.3t.fi/artikkeli/uutiset/teknologia/verkossa_ei_ole_turvallisia_maita_vain_yksi_tapa_suojaa_urkinnalta
Tomi says:
This information iPhone, Lumia and Android phones transmit the United States
Calls, text messages, location information – a lot of things, including U.S. intelligence agencies can apparently be accessed. Also the Finnish smartphone data is likely to be achieved if desired.
The U.S. intelligence community NSA can get your hands on the most popular smartphone data. About a week ago revealed that, among other things, Microsoft, Google and Apple have given the NSA for information about users of their services.
Leak shows that NSA has a firm grip on smartphones, as Apple, Google and Microsoft share the majority of the smartphone market.
What information you can get from the mobile phone?
1 Who is calling you, and because
Google can store your data on Android phones for calls.
2 Address and credit card number
If you register as Apple, Google or Microsoft’s application store, he must notify his name and address, phone and other contact details and credit card numbers.
3 With your contact information
The companies also offer cloud services, which can back up your phone content.
4 Your text message
Google can save Android users, at least for SMS routing information. Windows Phone 8, Phone users can activate the automatic backup,
Apple again seeks to replace the text in their own iMessage service.
US-based servers.
5 Where you are and move
As well as Google, Apple and Microsoft for example, store a user’s location from the map or the other Services.
6 Your photos
Photos may also include location information, so they can be transmitted with the data, where they were taken.
7 Web browsing and search
The companies will also record the websites you visit to your phone’s browser. Google will also save your searches times. So does Microsoft’s Bing search service.
8 Your speech, your nickname and family tree
Apple iPhone’s Siri voice-hour service for the spoken word will be sent to Apple. At the same time Apple Siri can be stored in the interest of users and nicknames, address book contacts, nicknames, as well as the relations between persons.
Also, Windows Phone, voice recognition
9 Your phone’s model and the unique identifier
10, Almost everything else
If Apple’s iPhone, the user accepts the diagnostics and user data collection
Source: http://www.digitoday.fi/tietoturva/2013/06/15/nama-tiedot-iphone–lumia–ja-android-puhelimet-valittavat-yhdysvaltoihin/20138379/66?rss=6
Tomi Engdahl says:
NSA-proof encryption exists. Why doesn’t anyone use it?
http://www.washingtonpost.com/blogs/wonkblog/wp/2013/06/14/nsa-proof-encryption-exists-why-doesnt-anyone-use-it/?wprss=rss_ezra-klein
Computer programmers believe they know how to build cryptographic systems that are impossible for anyone, even the U.S. government, to crack. So why can the NSA read your e-mail?
Last week, leaks revealed that the Web sites most people use every day are sharing users’ private information with the government. Companies participating in the National Security Agency’s program, code-named PRISM, include Google, Facebook, Apple and Microsoft.
It wasn’t supposed to be this way. During the 1990s, a “cypherpunk” movement predicted that ubiquitous, user-friendly cryptographic software would make it impossible for governments to spy on ordinary users’ private communications.
The government seemed to believe this story, too. “The ability of just about everybody to encrypt their messages is rapidly outrunning our ability to decode them,” a U.S. intelligence official told U.S. News & World Report in 1995. The government classified cryptographic software as a munition, banning its export outside the United States. And it proposed requiring that cryptographic systems have “back doors” for government interception.
The cypherpunks won that battle. By the end of the Clinton administration, the government conceded that the Internet had made it impossible to control the spread of strong cryptographic software.
But more than a decade later, the cypherpunks seem to have lost the war. Software capable of withstanding NSA snooping is widely available, but hardly anyone uses it. Instead, we use Gmail, Skype, Facebook, AOL Instant Messenger and other applications whose data is reportedly accessible through PRISM.
And that’s not a coincidence: Adding strong encryption to the most popular Internet products would make them less useful, less profitable and less fun.
“Security is very rarely free,” says J. Alex Halderman, a computer science professor at the University of Michigan. “There are trade-offs between convenience and usability and security.”
Most people’s priority: Convenience
Consumers have overwhelmingly chosen convenience and usability. Mainstream communications tools are more user-friendly than their cryptographically secure competitors and have features that would be difficult to implement in an NSA-proof fashion.
And while most types of software get more user-friendly over time, user-friendly cryptography seems to be intrinsically difficult. Experts are not much closer to solving the problem today than they were two decades ago.
Most modern online services do make use of encryption. Popular Web services such as Gmail and Hotmail support an encryption standard called SSL.
But while this kind of encryption will protect users against ordinary bad guys, it’s useless against governments.
That’s because SSL only protects data moving between your device and the servers operated by Google, Apple or Microsoft. Those service providers have access to unencrypted copies of your data. So if the government suspects criminal behavior, it can compel tech companies to turn over private e-mails or Facebook posts.
That problem can be avoided with “end-to-end” encryption. In this scheme, messages are encrypted on the sender’s computer and decrypted on the recipient’s device. Intermediaries such as Google or Microsoft only see the encrypted version of the message, making it impossible for them to turn over copies to the government.
Software like that exists. One of the oldest is PGP, e-mail encryption software released in 1991.
Others include OTR (for “off the record”), which enables secure instant messaging, and the Internet telephony apps Silent Circle and Redphone.
But it’s difficult to add new features to applications with end-to-end encryption. Take Gmail, for example. “If you wanted to prevent government snooping, you’d have to prevent Google’s servers from having a copy of the text of your messages,” Halderman says. “But that would make it much harder for Google to provide features like search over your messages.” Filtering spam also becomes difficult. And end-to-end encryption would also make it difficult for Google to make money on the service, since it couldn’t use the content of messages to target ads.
A similar point applies to Facebook. The company doesn’t just transmit information from one user to another.
These features depend on Facebook’s servers having access to a person’s private data, and it would be difficult to implement them in a system based on end-to-end encryption.
Other user headaches
End-to-end encryption creates other headaches for users. Conventional online services offer mechanisms for people to recover lost passwords. These mechanisms work because Apple, Microsoft and other online service providers have access to unencrypted data.
In contrast, when a system has end-to-end encryption, losing a password is catastrophic; it means losing all data in the user’s account.
Also, encryption is effective only if you’re communicating with the party you think you’re communicating with. This security relies on keys — large numbers associated with particular people that make it possible to scramble a message on one end and decode it on the other. In a maneuver cryptographers call a “man in the middle” attack, a malicious party impersonates a message’s intended recipient and tricks the sender into using the wrong encryption key.
“A key is supposed to be associated closely with a person, which means you want a person to be involved in creating their own key, and in verifying the keys of people they communicate with,” says Ed Felten, a computer scientist at Princeton University. “Those steps tend to be awkward and confusing.”
PGP “is not usable enough to provide effective security for most computer users,”
Users expect software to “just work” without worrying too much about the technical details. But the researchers discovered that users tended to make mistakes that compromise their security. Users are supposed to send other people their “public key,” used to encode messages addressed to them, and to keep their private key a secret. Yet some users foolishly did the opposite
Using PGP is such a hassle that even those with a strong need for secure communication resist its use. When Edward Snowden, the man who leaked the details of the PRISM program, first contacted Glenn Greenwald at the Guardian in February, he asked the journalist to set up PGP on his computer so the two could communicate securely. He even sent Greenwald a video with step-by-step directions for setting up the software. But Greenwald, who didn’t yet know the significance of Snowden’s leaks, dragged his feet.
He did not set up the software until late March, after filmmaker Laura Poitras, who was also in contact with Snowden, met with Greenwald and alerted him to the significance of his disclosures.
Halderman isn’t optimistic that strong cryptography will catch on with ordinary users anytime soon. In recent years, the companies behind the most popular Web browsers have beefed up their cryptographic capabilities, which could make more secure online services possible. But the broader trend is that users are moving more and more data from their hard drives to cloud computing platforms, which makes data even more vulnerable to government snooping.
Strong cryptographic software is available to those who want to use it. Whistleblowers, dissidents, criminals and governments use it every day. But cryptographic software is too complex and confusing to reach a mass audience anytime soon. Most people simply aren’t willing to invest the time and effort required to ensure the NSA can’t read their e-mail or listen to their phone calls. And so for the masses, online privacy depends more on legal safeguards than technological wizardry.
Tomi Engdahl says:
Edward Snowden says ‘the truth is coming,’ but when will we see the rest of his evidence?
http://www.theverge.com/2013/6/17/4437960/edward-snowden-nsa-question-answer-prism
“The US government is not going to be able to cover this up by jailing or murdering me,” Snowden said, opening the session with melodrama. “Truth is coming, and it cannot be stopped.”
Snowden repeated publicly known facts, reiterating that more information about how PRISM works will be revealed in the future.
When asked about counter-surveillance measures, Snowden affirmed that encryption can help safeguard against NSA spying. “Properly implemented strong crypto systems are one of the few things that you can rely on,” Snowden said. “Unfortunately, endpoint security is so terrifically weak that NSA can frequently find ways around it.”
Tomi Engdahl says:
How Web mail providers leave door open for NSA surveillance
http://news.cnet.com/8301-13578_3-57590389-38/how-web-mail-providers-leave-door-open-for-nsa-surveillance/
Protecting users’ e-mail privacy from the National Security Agency and other intelligence services means using encryption. But with the exception of Google, few companies do everything they can.
Over the last decade or so, Web mail providers began to turn on encryption to armor the connections between users’ computers and Gmail, Yahoo Mail, Hotmail and other services.
But during the next step, when those e-mail messages are transferred from one company’s servers to another’s, they’re rarely encrypted.
“The incentives aren’t really there for companies to try to implement it,”
A survey of top mail providers shows that Google is alone in using strong encryption, known as SMTP-TLS, to fully armor e-mail connections for its users, as long as the other company’s server is willing to encrypt as well. SMTP-TLS also protects employee e-mail at security-conscious companies, large law firms, and sensitive government agencies including the NSA, the White House, and the Department of Homeland Security. (You can check on your own provider by typing in your e-mail address at CheckTLS.com.)
Unfortunately, those are the exceptions. Facebook, Hotmail, Yahoo Mail, and AOL Mail do not accept incoming e-mail in SMTP-TLS encrypted form, meaning hundreds of millions of users’ private communications are vulnerable to monitoring. Both the sending and receiving servers must have encryption turned on for a secure connection to happen.
One reason why so many mail providers don’t encrypt server-to-server mail links using SMTP-TLS is that, unlike browser encryption, this security precaution would be invisible to users. And the fat pipes that backbone providers provide have historically been viewed as safe. (SMTP-TLS stands for Simple Mail Transfer Protocol Transport Layer Security. TLS was published as an Internet protocol in 1999.)
click here says:
It is really an incredible and handy section of info. I will be satisfied that you distributed this helpful information and facts with us. You should remain you informed like that. Thank you for giving.
Tomi Engdahl says:
Stop Watching Us.
https://optin.stopwatching.us/
The revelations about the National Security Agency’s surveillance apparatus, if true, represent a stunning abuse of our basic rights. We demand the U.S. Congress reveal the full extent of the NSA’s spying programs.
Unwarranted government surveillance is an intrusion on basic human rights that threatens the very foundations of a democratic society.
Tim Berners Lee Wired
Dear Members of Congress,
We write to express our concern about recent reports published in the Guardian and the Washington Post, and acknowledged by the Obama Administration, which reveal secret spying by the National Security Agency (NSA) on phone records and Internet activity of people in the United States.
Tomi Engdahl says:
Why Snowden Asked Visitors in Hong Kong to Refrigerate Their Phones
http://thelede.blogs.nytimes.com/2013/06/25/why-snowdens-visitors-put-their-phones-in-the-fridge/
Before a dinner of pizza and fried chicken late Sunday in Hong Kong, Edward J. Snowden insisted that a group of lawyers advising him in the Chinese territory “hide their cellphones in the refrigerator of the home where he was staying, to block any eavesdropping,” as my colleague Keith Bradsher reported.
Why a refrigerator? The answer does not, as some might assume, have anything to do with temperature. In fact, it does not matter particularly if the refrigerator was plugged in. It is the materials that make up refrigerator walls that could potentially turn them into anti-eavesdropping devices.
“What you want to do is block the radio signals which could be used to transmit voice data, and block the audio altogether,” Adam Harvey, a designer specializing in countersurveillance products explained. Refrigerators made from metal with thick insulation could potentially do both, he says, regardless of whether it is mild or icy within.
Another household object that functions similarly, Mr. Harvey has learned through his research into cellphone data transmission, is a stainless steel martini shaker.
“It’s a perfect Faraday cage – it will block all radio signals unless you decide you need to pour yourself a martini,”
Blocking data transmission, of course, is a different issue from muffling audio. Although a thick refrigerator door is good at masking sound (as anyone who has lost a cat inside one knows), soundproofing is not necessarily integral to its design.
why not just ask everyone to turn off his phone and remove the batteries? Beyond the fact that many phones these days do not easily enable battery removal, identifying a pure off is complicated.
Battery removal can be equally deceptive. Even once one figures out how to extract the primary battery, there may be additional power sources within the apparatus.
Tomi Engdahl says:
A simple SSL tweak could protect you from GCHQ/NSA snooping
It might slow you down, but hey, you can’t have everything
http://www.theregister.co.uk/2013/06/26/ssl_forward_secrecy/
An obscure feature of SSL/TLS called Forward Secrecy may offer greater privacy, according to security experts who have begun promoting the technology in the wake of revelations about mass surveillance by the NSA and GCHQ.
Several key exchange mechanisms exist but the most widely used mechanism is based on the well-known RSA algorithm
This approach relies on the server’s private key to protect session keys.
“This is an efficient key exchange approach, but it has an important side-effect: anyone with access to a copy of the server’s private key can also uncover the session keys and thus decrypt everything,” Ristic warns
This capability makes it possible for enterprise security tools – such as intrusion detection and web application firewalls – to screen otherwise undecipherable SSL encrypted traffic, given a server’s private keys. This feature has become a serious liability in the era of mass surveillance.
The NSA also carries out deep packet inspection analysis of traffic passing through US fibre optic networks
The upshot is that intelligence agencies are collecting all the traffic they can physically capture before attempting to snoop upon encrypted content, where possible. These techniques are currently only practical for intelligence agencies but this may change over time
“Your adversaries might not have your private key today, but what they can do now is record all your encrypted traffic,” Ristic explains. “Eventually, they might obtain the key in one way or another – for example, by bribing someone, obtaining a warrant, or by breaking the key after sufficient technology advances. At that point, they will be able to go back in time to decrypt everything.”
The Diffie–Hellman protocol offers an alternative algorithm to RSA for cryptographic key exchange. Diffie–Hellman is slower but generates more secure session keys that can’t be recovered simply by knowing the server’s private key, a protocol feature called Forward Secrecy.
“Breaking strong session keys is clearly much more difficult than obtaining servers’ private keys, especially if you can get them via a warrant,” Ristic explains. “Furthermore, in order to decrypt all communication, now you can no longer compromise just one key – the server’s – but you have to compromise the session keys belonging to every individual communication session.”
Someone with access to the server’s private key can perform an active man-in-the-middle attack and impersonate the target server. However, they can do that only at the time the communication is taking place. It is not possible to pile up mountains of encrypted traffic for later decryption. So, Forward Secrecy still creates a significant obstacle against industrial scale snooping.
SSL supports Forward Secrecy using two algorithms: Diffie-Hellman (DHE) and the adapted version for use with Elliptic Curve cryptography (ECDHE).
“Although the use of Diffie-Hellman key exchange eliminates the main attack vector, there are other actions a powerful adversary could take,” Ristic warns. “For example, they could convince the server operator to simply record all session keys.”
“Server-side session management mechanisms could also impact Forward Secrecy.”
gestionar redes sociales says:
Many thanks for the great writeup. It was some sort of leisure time profile that. Start looking complicated to help way unveiled gratifying of your stuff! Nonetheless, exactly how should we communicate?
facebook fan page says:
Wow, this piece of writing is fastidious, my sister is analyzing these kinds of things, so I am going to tell her.
Tomi Engdahl says:
TOR Project: Stop using Windows, disable JavaScript
http://www.itworld.com/software/367979/tor-project-stop-using-windows-disable-javascript
The anonymizing network gives some advice following a startling Firefox zero-day vulnerability
he TOR Project is advising that people stop using Windows after the discovery of a startling vulnerability in Firefox that undermined the main advantages of the privacy-centered network.
The zero-day vulnerability allowed as-yet-unknown interlopers to use a malicious piece of JavaScript to collect crucial identifying information on computers visiting some websites using The Onion Router (TOR) network.
“Really, switching away from Windows is probably a good security move for many reasons,” according to a security advisory posted Monday by The TOR Project.
The TOR Project’s reasoning comes from the characteristics of the malicious JavaScript that exploited the zero-day vulnerability. The script was written to target Windows computers running Firefox 17 ESR (Extended Support Release), a version of the browser customized to view websites using TOR.
People using Linux and OS X were not affected, but that doesn’t mean they couldn’t be targeted in the future. “This wasn’t the first Firefox vulnerability, nor will it be the last,” The TOR Project warned.
The JavaScript was likely planted on certain websites that the attacker wanted to see who came to visit. The script collected the hostname and MAC (Media Access Control) address of a person’s computer and sent it to a remote computer, the exact kind of data that TOR users hope to avoid revealing while surfing the Internet.
Tomi Engdahl says:
Email Company Reportedly Used By Edward Snowden Shuts Down Rather Than Hand Data Over To Feds
http://www.forbes.com/sites/kashmirhill/2013/08/08/email-company-reportedly-used-by-edward-snowden-shuts-down-rather-than-hand-data-over-to-feds/
When Edward Snowden emailed journalists and activists in July to invite them to a briefing at the Moscow airport during his long stay there, he used the email account “[email protected]” according to one of the invitees. Texas-based Lavabit came into being in 2004 as an alternative to Google’s Gmail, as an email provider that wouldn’t scan users’ email for keywords. Being identified as the provider of choice for the country’s most famous NSA whistleblower led to a flurry of attention for Lavabit and its encrypted email services, from journalists, and also, apparently, from government investigators. Lavabit founder Ladar Levison announced Thursday that he’s shutting down the company rather than cooperating with a government investigation (presumably into Snowden).
“I have been forced to make a difficult decision: to become complicit in crimes against the American people or walk away from nearly ten years of hard work by shutting down Lavabit,” writes Levison. “After significant soul searching, I have decided to suspend operations.”
Tomi Engdahl says:
Silent Circle Preemptively Shuts Down Encrypted Email Service To Prevent NSA Spying
http://techcrunch.com/2013/08/08/silent-circle-preemptively-shuts-down-encrypted-email-service-to-prevent-nsa-spying/
“We knew USG would come after us”. That’s why Silent Circle CEO Michael Janke tells TechCrunch his company shut down its Silent Mail encrypted email service. It hadn’t been told to provide data to the government, but after Lavabit shut down today rather than be “complicit” with NSA spying, Silent Circle told customers it has killed off Silent Mail rather than risk their privacy.
The Silent Circle blog posts explains “We see the writing the wall, and we have decided that it is best for us to shut down Silent Mail now.” It’s especially damning considering Silent Circle’s co-founder and president is Phil Zimmermann, the inventor of widely-used email encryption program Pretty Good Privacy.
Silent Circle reportedly had revenue increase 400% month-over-month in July after corporate enterprise customers switched to its services in hopes of avoiding surveillance.
Silent Circle’s other secure services including Silent Phone and Silent Text will continue to operate as they do all the encryption on the client side within users’ devices. But it explained that “Email that uses standard Internet protocols cannot have the same security guarantees that real-time communications has.”
tall says:
Hi there terrific website! Does running a blog
like this require a lot of work? I’ve no knowledge of
programming however I was hoping to start my own blog
soon. Anyhow, should you have any recommendations or tips for
new blog owners please share. I understand this is off subject but I
simply had to ask. Cheers!
Tomi Engdahl says:
AppDirect raises $9M, acquires Standing Cloud to help businesses adopt a hybrid network in the NSA’s wake
http://pandodaily.com/2013/09/10/appdirect-raises-9m-acquires-standing-cloud-to-help-businesses-adopt-a-hybrid-network-in-the-nsas-wake/
The revelations have led to questions concerning the safety of many US-based technology services, with some suggesting that consumers should boycott or avoid companies based in the country, whether they’ve been implicated in the leaks or not. (Many companies are unable to reveal government requests.)
The acquisition will allow AppDirect to better serve businesses seeking to use a privately-hosted cloud infrastructure instead of relying on public clouds. Daniel Saks, the company’s chief executive, says that this capability will become increasingly important as businesses adopt hybrid infrastructures which rely on both privately-and publicly-hosted networks.
“People are certainly more afraid of the cloud for certain things but are embracing it for others,” Saks says. “Our response to that is, let’s give customers options.”
US-based cloud networks have advantages over private networks, Saks says — namely that they can be more reliable and easier to scale. Privately-hosted networks, meanwhile, are often seen as more secure and less likely to be tampered with by the US government. Hybrid solutions are meant to offer the best of both set-ups.
“Businesses need to make the choice that their data is confidential and that it needs added security,” Saks says. They can use a private network to host that data, he says; for other information and services they can use public networks.
That approach is riddled with potentially — or perhaps probably — faulty assumptions, of course. Most of us are unaware of the NSA and other government agencies’ ability to gather information from anything connected to the Internet, whether it’s a smartphone or a privately-hosted network.
Relying on a private network to keep data secure is like hoping that encryption will protect your communications or that a blanket will ward off nightmarish creatures in the middle of the night: it might make some businesses and citizens feel better, but it’s unlikely to make much of a difference in practice.
nokia tracking says:
Good day very nice site!! Man .. Excellent .. Superb ..
I will bookmark your site and take the feeds also?
I am glad to search out so many useful information right here in the submit, we want work out more strategies on this regard, thank
you for sharing. . . . . .
http://twitter.com/BurkeStrobel says:
Paragraph writing is also a excitement, if you know then you can write or else it is complicated to write.
wedding stationery says:
Hey there pleasant blog site! Guy. Excellent. Superb. I’m going to book mark your web site and go ahead and take rss feeds as well? I am just content to locate quite a few helpful facts listed here from the placed, we’d like develop additional tactics within this regard, thanks for spreading.
fujitsu air conditioning says:
Fastidious replies in return of this question
with firm arguments and explaining everything concerning that.
Tomi Engdahl says:
How to foil the NSA and GCHQ with strong encryption
Column Now is the time to secure your communications
http://www.theinquirer.net/inquirer/opinion/2331668/how-to-foil-the-nsa-and-gchq-with-strong-encryption
THE MOST INTERESTING DEVICE shown at Mobile World Congress (MWC) in Barcelona this week was the secure Blackphone developed by Silent Circle and Geeksphone.
The Blackphone features anonymous search, automatic disabling of non-trusted WiFi hotspots, and private texting, calling and file transfer capabilities. It’s available to the general public, and bundles additional security features that apparently go beyond the basic messaging security provided by Blackberry to enterprise customers in its Blackberry Messaging (BBM) service.
Whether or not you’re interested in the Blackphone to secure your phone calls and messages from unwarranted snooping by government intelligence agencies in the US, UK and elsewhere, there are other measures you can take to keep your private communications secure from the prying Five Eyes and others, and these have become easier to use in recent years.
There’s Pretty Good Privacy (PGP) for email as implemented by the OpenPGP Alliance and the GnuPG project for all major operating systems, including Windows, Mac OS X, Linux, BSD, Android and iOS. There are also a number of secure email service providers.
For online chat, there’s the Off The Record (OTR) plugin for Pidgin with several implementations.
Tomi Engdahl says:
Who Has Your Back? 2014: Protecting Your Data From Government Requests
https://www.eff.org/who-has-your-back-government-data-requests-2014
We entrust our most sensitive, private, and important information to technology companies like Google, Facebook, and Verizon. Collectively, these companies are privy to the conversations, photos, social connections, and location data of almost everyone online. The choices these companies make affect the privacy of every one of their users. So which companies stand with their users, embracing transparency around government data requests? Which companies have resisted improper government demands by fighting for user privacy in the courts and on Capitol Hill? In short, which companies have your back?
These questions are even more important in the wake of the past year’s revelations about mass surveillance, which showcase how the United States government has been taking advantage of the rich trove of data we entrust to technology companies to engage in surveillance of millions of innocent people in the US and around the world.
Tomi Engdahl says:
The Only Email System The NSA Can’t Access
http://www.forbes.com/sites/hollieslade/2014/05/19/the-only-email-system-the-nsa-cant-access/
When the NSA surveillance news broke last year it sent shockwaves through CERN, the particle physics laboratory in Switzerland. Andy Yen, a PhD student, took to the Young at CERN Facebook group with a simple message: “I am very concerned about the privacy issue, and I was wondering what I could do about it.”
Encrypted emails have actually been around since the 1980s, but they are extremely difficult to use. When Edward Snowden asked a reporter to use an end-to-end encrypted email to share details of the NSA surveillance program the reporter couldn’t get the system to work, says Yen.
physics to found ProtonMail, a gmail-like email system which uses end-to-end encryption, making it impossible for outside parties to monitor.
“We encrypt the data on the browser before it comes to the server,” he explains. “By the time the data comes to the server it’s already encrypted
While half the team is now at MIT, some are still in Switzerland where the ProtonMail’s servers are housed for extra protection.
Yen has turned down venture capital firms looking to invest in ProtonMail.
ProtonMail’s revenue model is similar to something like Dropbox – charging only for extra storage.
“One of our motivations was human rights,” says Yen. “Having privacy is very important from a freedom of speech standpoint.”
The paid accounts will be $5/month and will provide 1GB of storage.
seo new york says:
There is certainly a lot to learn about this subject.
I love all of the points you’ve made.
bing.com says:
Hi! Do you know if they make any plugins to safeguard against hackers?
I’m kinda paranoid about losing everything I’ve worked hard on. Any recommendations?