Year 2014 is coming to end, so it is time to look forward what to expect from year 2015 in cyber security.
Cyber security will get harder year y year. Year 2014 was much worse than 2013. Heartbleed, Bash, and POODLE vulnerabilities were just the beginning of what to expect in 2015. I expect that year 2014 was easy compared to what year 2015 will be. 2015 will prove to be a challenging year for IT security professional. Attacks can happen anywhere and anytime and they don’t have to be major attacks by nation states. They could come from inside or outside.
According to Gartner and Securityweek Total information security spending will grow a further 8.2 percent in 2015 to reach $76.9 billion. Unfortunately, security investments are not keeping up with IT enhancements that are continuously widening our attack surface and making systems more vulnerable. As computer software has become the backbone of modern civilization, “hacktivists”, organized cyber criminals, state-sponsored cyber attackers, and terrorist organizations try to exploit design flaws and weaknesses in the applications in order to embarrass corporations and government agencies, and commit fraud.
The steady flow of software security issues will be making headlines also in 2015. Serious security flaws will be found on both open seurce and proprietary software.
There are many people looking for a good process to develop secure software, because after-the-fact band-aiding is not a sustainable approach. If the same methods continue to be used to develop the software, retrospectively adding tests, then there will only be a very modest reduction in the flow of problems. Processes exist but have yet to be broadly applied for developing reliable and secure networking software. Traditional methods used to develop software continue to result in high failure rates. Why create insecure security?
Year 2014 was a year of cybersecurity after the NSA revelations made in 2013. There were lots of articles related to the material published. Not everything has yet been published, so I would expect some new NSA revelations details to be published also in 2015. So I expect some new information leaks on how govermential security organizations spy us all.
It seems like year 2014 has almost been “The Year of PoS Breaches.” Can We Learn from Big Breaches? At least companies will also face more stringent regulations: The new Payment Card Industry Data Security Standard 3.0 (PCI 3.0) will be mandatory for all businesses that store, process or transmit payment card information beginning 1 January 2015. The revamped standard includes requirements aimed at third party providers. The changes follow a string of high profile breaches – companies will also face more stringent regulations: The new Payment Card Industry Data Security Standard 3.0 (PCI 3.0) will be mandatory for all businesses that store, process or transmit payment card information beginning 1 January 2015. The revamped standard includes requirements aimed at third party providers. I expect that those new requirements do not result any quick change to the situation. As more and more breach reports have come up constantly, consumers officially are starting to get breach fatigue and banks are bringing breached companies to court to pay for damages caused to them.
Public and private organizations are facing an increasing frequency and sophistication of cyber-attacks and security breaches – many of which are only discovered after the fact. McAfee Labs’ 2015 Threats Predictions report is an eye-opening read which forecasts increased levels of crime, espionage and warfare operations. Cybercriminals are expected to use more sophisticated methods to remain hidden on a victim’s network, carrying out long-term theft of data without detection.
Get Ready For The Hack Attack That Drives A Big Company Out Of Business article predicts that 2015 will be the year that some company goes out of business because they didn’t plan adequately for an attack. In the past, the most sophisticated hacks against companies were carried out by big nation-states or criminal organizations. In year 2014 the Sony Pictures hack happened and showed that motives of sophisticated hackers have changed from self-gain to destruction. Many company officers are only now becoming aware of the threat (boards of directors and C-level officers have traditionally been focused on other threats). A computerized attack can cause a lot of damage to a well prepared company, and can turn a not so well prepared company to a complete disaster it can’t recover. Sony attack opens new doors of risks in the areas of corporate extortion.
As Internet of Thigs becomes more and more used, it will be more hacked. Thus security of Internet of Things will be more and more talked about. IoT os one field where cyber security flaws can kill. The European Police Office (Europol) said governments are ill-equipped to counter the menace of “injury and possible deaths” spurred by hacking attacks on critical safety equipment. There are many potential dangers are in transportation: many new cars are Internet connected and potentially vulnerable, SCADA Systems in Railways Vulnerable to Attack and Airline bosses ignore cyber security concerns at their peril. Whether it is an unintentional cyber incident or a deliberate attack, security continues to be a vital part of the automation industry and it will remain, with safety, a growing area of concern for manufacturers in the coming years. Security awareness is on the rise throughout the industry. Security is becoming a business enabler that can provide manufacturers more than just an insurance policy.
Soon, almost every network will soon have IoT-hacking in it. IDC predicts that in two years from 90 per cent of the global IT networks have met IoT data theft. In a report, cybersecurity firm Fortinet expects greater threats from “denial of service attacks on assembly line, factory, industrial control systems, and healthcare and building management…resulting in revenue losses and reputation damages for organizations globally.” This opens new doors of risks in the areas of corporate extortion, altering of corporate business operations, and the extension of cyberattacks to include physical threats of harm to civilians.
Why cyber warfare is becoming more and more attractive to small nations and terrorist groups. Enabled by Internet connectivity, cyber war provides more bang for the buck than investment in conventional weapons. It is cheaper for and far more accessible to these small nation-states than conventional weapons . It allows these countries to pull off attacks without as much risk of getting caught and without the repercussions when they are caught. There are many reasons why a nation-state or non-nation entity would pursue a cyber war program, and today many countries large and small invest in cyber warfare. Recent cyber attacks suggest that fewer resources are required to wage an attack than to defend against one. As the whole world gets connected, it just provides the details that make these attacks possible. In the not-too-distant future, warfare with traditional weaponry may take a backseat to potentially more destructive tactics: computer code attacking the companies and infrastructures, including electric grids and oil and gas pipelines, that society relies on.
It was estimated that first online murder would happen in 2014. It did not seem to happen in 2014 as far as I know. I think that is likely that online murder can happen in 2015. There are tools available for this to happen. Cyber-murder it can happen without us knowing about it.
Mobile devices will be one of the focal points for cyber-attackers in 2015, as they present relatively easy, low-risk points of entry that can be monitored remotely for passwords, account numbers, and personal identification data. Sure, there are still relatively easy to publish malicious application stores. Within next year advanced mobile exploit kits will become available.
Mobile devices will start to play part in denial of service attacks. Vietnam, India and Indonesia will be the distributed denial of service volcanoes of next year due to the profieration of pwned mobiles.
Year 2014 brought encryption to mainstream smart phones (new encryption features from Apple Inc. and Google Inc). In year 2015 government organizations try to tackle a very modern problem: password-protected encrypted cellphones. It will be a fight on surveillance as everyone starts to implement encryption.
Long predicted but always seeming to be “just around the corner,” mobile payments may finally have arrived. The coming mobile payment revolution, the underlying technologies – and alternative solutions – have been emerging for some time. Technologies playing a supporting role in this shift include encryption advances, digital currencies, biometrics, NFC, Bluetooth, QR codes, and even the use of sound wave data transfer. There will also bea products mrketed to prevent different kind of potential threats the new technologies can cause.
There is a never-ending battle between good and evil in the cyber world. Various types of attacks are successful because they are well-disguised, blend different techniques, and constantly evolve. You need Layered Security – It’s Not Just for Networks. Use a layered security architecture that supports a combination of defenses in ways attackers don’t expect and that continuously evolves protections to keep up with dynamic attacks. Traditionally these approaches have been focused on the network, but they can and should be applied to other parts of IT system as well (start from email gateways). Email is the preferred channel for business communications and thus continues to be a vector of choice for attackers.
Threat Information Sharing Will Become Necessary for Survival. Security controls (SANS critical controls, ISO/IEC 27002, NIST Cybersecurity Framework, and the Cloud Controls Matrix) are safeguards and counteract or minimize security risks relating to digital property. The more you can automate a control, the better off you will be. We are in the way of Moving towards an adaptive and automated way of applying intelligence based on behavior and heuristics is clearly moving in the right direction to enable a more actionable and relevant set of controls. Threat intelligence coming from a variety of sources (security companies, the government and the open source community) is needed. Key to the success is publishing intelligence in a variety of data structures (STIX, TAXI and other standard industry formats) to best describe threats in a way that can be aggregated and understood by others.
More and more organizations are moving applications and data to IaaS/PaaS environments. Many enterprise IT departments have reason for concern: industry experts agree that moving sensitive data into the hands of third-party cloud providers expands and complicates the risk landscape in which companies operate every day. You need to understand cloud database security basics and more.
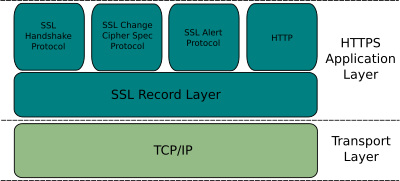
Today major players are embracing end-to-end encryption, so that about 50% of web traffic is carried by HTTPS. HTTPS-everywhere will get boost in 2015 as a new certificate authority – backed by big names on the internet including Mozilla, Cisco and Akamai – plans to offer SSL certs at no charge starting summer 2015. This move will make it even more easier for people to run encrypted, secure HTTPS websites.
Google is proposing to warn people their data is at risk every time they visit websites that do not use the “HTTPS” system. If implemented, the change would mean that a warning would pop-up when people visited a site that used only HTTP to notify them that such a connection “provides no data security”. In the short term, the biggest headache is likely to be faced by website operators who will feel forced to migrate unencrypted HTTP websites to encrypted HTTPS.
You can’t trust that normal web security technologies will guarantee safety. Your HTTPS security will be more manipulated than before. End to end HTTPS is generally good security addition to end users, but it does not solve all the problems. The increased use of HTTPS has made the life of IT departments harder, because normal firewalls can’s look what is inside encypted HTTPS packets, so they can’t block potential security treads that are carried within HTTPS packets. There are some special corporate firewall arrangements that can intercept HTTPS traffic (they do kind of man-in-the middle attack that decrypts and encryps the packets on the way). So SSL communications can be intercepted and broken.


3,110 Comments
Routerlogin.net says:
hye..very nice article. very well written. ipleased to read it..u defined very thing in very good manner. thank you for this wonderful Article.
smackdown real or fake says:
thanks for sharing this stuff
MS OneNote Support says:
Awesome Post!
vier says:
I’m not sure exactly why but tһis blog is loading incredibly slow for me.
Is anyone eⅼse havіng this problem or is it a problеm
on my end? I’ll check back later and sеe if the problem still exists.
http://netgeargeniesupport.com says:
nice post….
routerlogin
netgear router password
routerlogin.net
Router Login says:
nice post.
routerlogin admin page
Clickbank Products Rotators says:
Simply wish to say your article is as amazing. The clarity on your post
is simply spectacular and that i can think you’re knowledgeable in this subject.
Well together with your permission allow me to snatch your feed
to stay updated with approaching post. Thank you a million and please carry on the gratifying work.
it company in surat says:
Trueline Solution is one of The Best IT Company in Surat, Gujarat, and India. We are leading seo service provider in surat.
eshas says:
!Hi
thank you for this. i love to read and support authors as much as i can. they play such an important role in our society and civilization especially the good ones you offer some great ideas supporting these wonderful people…
http://degitally.com/