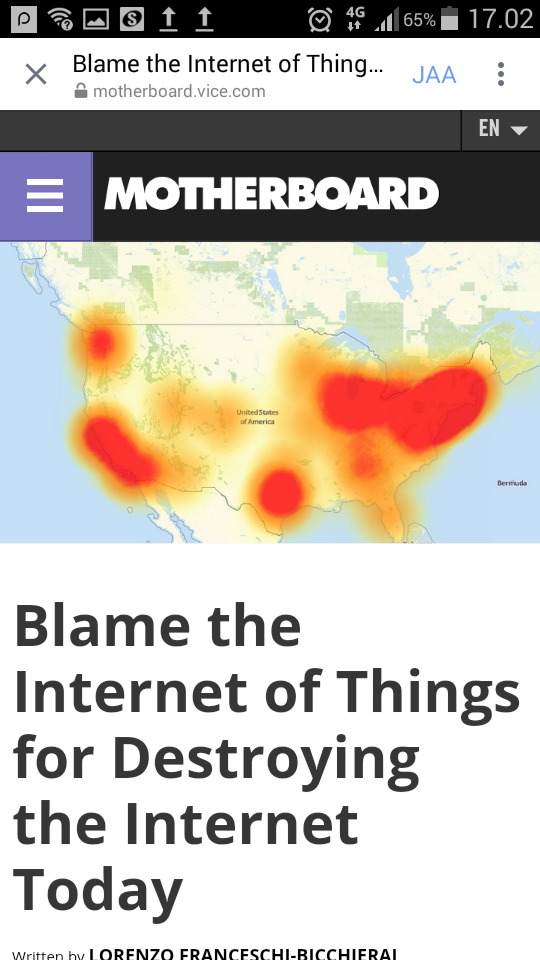
A massive botnet of hacked Internet of Things devices has been implicated in the cyberattack that caused a significant internet outage on Friday.
The botnet, which is powered by the malware known as Mirai, is in part responsible for the attack that intermittently knocked some popular websites offline, according to Level 3 Communications, one of the world’s largest internet backbone providers, and security firm Flashpoint.
On Friday morning, someone targeted Dyn, a company that offers core internet services for popular websites such as Twitter, Spotify, Github, and many others. The attack mainly targeted Dyn’s Domain Name System (DNS) management services infrastructure on the East Coast of the United States, according to the company.
60 Comments
Tomi Engdahl says:
Sh… IoT just got real: Mirai botnet attacks targeting multiple ISPs
Now ZyXEL and D-Link routers from Post Office and TalkTalk under siege
http://www.theregister.co.uk/2016/12/02/broadband_mirai_takedown_analysis/
The Mirai botnet has struck again, with hundreds of thousands of TalkTalk and Post Office broadband customers affected. The two ISPs join a growing casualty list from a wave of assaults that have also affected customers at Deutsche Telekom, KCOM and Irish telco Eir over the last two weeks or so.
Problems at the Post Office and TalkTalk both began on Sunday and collectively affected hundreds of thousands of surfers. Similar attacks against thousands of KCOM broadband users around Hull that started about the same time targeted users of telco-supplied routers. Thousands of punters at the smaller ISP were left without a reliable internet connection as a result of the assault, which targeted routers from Taiwanese manufacturer ZyXEL.
It’s unclear who is responsible for the growing string of attacks on ISP customers across Europe or their motives. The mechanism of the attack is, however, all too clear. Hackers are using the infamous Mirai malware or one of its derivatives to wreak havoc. The IoT malware scans for telnet before attempting to hack into vulnerable devices, using a brute-force attack featuring 61 different user/password combinations, the various default settings of kit from various manufacturers. Up to 5m devices are up for grabs thanks to wide open management ports, according to some estimates.
Jean-Philippe Taggart, senior security researcher at Malwarebytes, said: “The leaked Mirai code, poorly secured remote administration on IoT devices, coupled with the recent availability of a Metasploit module to automate such attacks make for an ideal botnet recruitment campaign.
“So far, it seems the infection does not survive a reboot, but the malicious actors tend to disable access to the remote administration as part of the infection. This prevents the ISP from applying an update that would solve these issues. The botnet gains a longer life as users seldom reboot their routers unless they’re experiencing a problem.”
Other experts imply further attacks along the same lines are inevitable because the state of router security is poor and unlikely to improve any time soon.
“The current state of IoT security is in bad shape, and will get a whole lot worse before it gets any better. The Mirai botnet, which is powered by 100,000 IoT devices that are insecure by default, is just the most obvious and topical example.”
Tomi Engdahl says:
Sony’s cameras are subject to change to spy devices or join a bot network – a bad hole in 80 models
Vulnerability discovered by security company SEC Consult. The company’s researchers found that the devices were two separate hard-coded user account. The first was the camera’s web interface. It allows an attacker would have to use telnet connections to devices. Second user account allows the attacker in turn would have received through the camera administrator rights telnet connection.
SEC Consult researchers concluded that the password is hard coded
At the moment, it does not appear that the password would be broken, but it is only a matter of time, researchers say.
Cameras can be attacked either the local network or over the Internet, if the camera network interface is open to the external network. The camera taken over by a hacker could use the device as a starting point to attack deeper into the network, to feed their own camera or video spy camera. The cameras could also be incorporated into the bot net and use it for example to execute a denial of service attacks.
Sony has list of devices and software update:
Source: http://www.tivi.fi/Kaikki_uutiset/sonyn-kamerat-voivat-muuttua-vakoilulaitteiksi-tai-liittya-bottiverkkoon-paha-aukko-80-mallissa-6605337
More:
New firmware for network cameras
https://www.sony.co.uk/pro/article/sony-new-firmware-for-network-cameras
Tomi Engdahl says:
Big Switch takes big bet it can beat off big denial of service attacks
Yuge attacks. The best attacks. Terabit-scale attacks from internet things
http://www.theregister.co.uk/2016/12/07/big_switch_takes_big_bet_it_can_beat_off_big_attacks/
Big Switch Networks is taking aim at the kinds of IoT-based attacks that have rocked the Internet this year.
Headlining its BigSecure Architecture release today is a service chaining solution the company’s chief product officer Prashant Gandhi told Vulture South can scale up to deflect a terabit-scale attack in about ten minutes, but will also “give you the ability to survive for hours”.
For a purely volumetric attack, Gandhi said the software-defined networking (SDN) controller in the demilitarised zone (DMZ) can reconfigure the service chain “so the traffic is redirected to the [security] infrastructure for mitigation”.
The controller then uses flow-based policies and access control lists to tell switches to drop the attack traffic.
However, as we’ve seen in the attacks against Dyn’s domain name services and Krebsonsecurity.com, Mirai-based botnet attacks may be volumetric but they’re coming from a host of different source IP addresses – all those compromised Internet of Things devices.
“You can leverage a pool of x86 services,” Gandhi said. “The virtual machines can be scaled out, and the SDN allows the traffic to be distributed across the servers.”
Putting the defences in software on a bunch of x86 servers isn’t expensive, making it affordable to activate the defences only when they’re needed.
That’s where the fast response comes from, Gandhi said: it should be possible to activate, program, and validate the infrastructure within ten minutes or so when an attack is detected.
BigSecure arrives as part of the latest round of updates to Big Switch Networks’ Big Monitoring Fabric. A deployment comprises its Big Monitoring Fabric SDN controller; a BMF Service Node (a 40 Gbps to 150 Gbps Intel DPDK-based node that handles filtering, deep packet inspection, service flow inspection, and filtering); and a pool of x86 resources providing the network function virtualisation (NFV) tool farm.
Third party tools like A10 Networks threat protection are supported, and the whole lot’s designed to run on white-box Ethernet from outfits like Dell EMC and Edgecore Networks.
Tomi Engdahl says:
Backdoor Found in Many Sony Security Cameras
http://www.securityweek.com/backdoor-found-many-sony-security-cameras
Sony has released firmware updates for many of its security cameras to address a critical vulnerability that can be exploited to take control of the devices, including by botnets such as Mirai.
The flaw, discovered by IT security services and consulting company SEC Consult, affects 80 Sony SNC series IP cameras that feature the company’s IPELA ENGINE signal processing system. These professional products are used by many organizations worldwide, including by FIFA during the 2014 World Cup.
Tomi Engdahl says:
Sigh… ‘Hundreds of thousands’ of… sigh, web CCTV cams still at risk of… sigh, hijacking
It’s been two years and no patches, say researchers
http://www.theregister.co.uk/2016/12/07/ip_cameras_unpatched/
Amid ongoing malware infections of IoT gadgets and armies of commandeered gizmos attacking server, glaring security holes in web-connected CCTV cameras are going unpatched.
So say researchers with Cybereason, who claim a pair of high-profile vulnerabilities they spotted in surveillance cams two years ago have been completely ignored by vendors – thus leaving the door wide open for miscreants to hijack potentially “hundreds of thousands” of devices and use them for attacks.
Cybereason’s Amit Serper says he and fellow researcher Yoav Orot exploited flaws in off-the-shelf internet-connected cameras back in 2014 in an effort to show how poor IoT security was at the time.
Since then, Serper says, the bugs have not only gone unpatched, but the insecure code has popped up in network camera firmware shipped by dozens of manufacturers selling their weak wares on Amazon. The Cybereason pair finger VStarcam as one vendor of vulnerable kit.
https://www.cybereason.com/zero-day-exploits-turn-hundreds-of-thousands-of-ip-cameras-into-iot-botnet-slaves/
Tomi Engdahl says:
Two Hackers Appear To Have Created a New Massive Internet of Things Botnet
November 29, 2016 // 04:20 PM EST
http://motherboard.vice.com/read/two-hackers-new-mirai-internet-of-things-botnet-deutsche-telekom?trk_source=popular
The massive cyberattacks that in the last few weeks have crippled several popular services like Twitter and Spotify, the website of a noted security journalist, and many more, may be about to get worse.
Two hackers appear to have created a new powerful zombie army of hacked Internet of Things devices with a modified version of the infamous malware Mirai. The cybercriminals are offering the powerful botnet to anyone who’s willing to pay to launch crippling distributed denial of service (DDoS) cyberattacks.
Last month, unknown attackers intermittently knocked offline several popular websites like Twitter, Spotify and many others using Mirai, a now-widespread type of malware created to automatically scan the internet for easy-to-hack devices and turn them into bots that can launch DDoS attacks. Now, two cybercriminals claim to have improved Mirai to infect new devices—mostly routers. This new variant gives them the ability to potentially harvest hundreds of thousands, perhaps millions, of new bots, according to security researchers.
One of the two hackers behind this new Mirai variant said they have control over one million hacked devices.
“The original Mirai was easy to take, like candy from this kids,”
An independent security researcher known as MalwareTech, who’s also been monitoring Mirai attacks for weeks, said that the two hackers are now in control of 75 percent (roughly 400,000) of all Mirai devices on the internet. Dale Drew, the chief security officer at Level 3 Communications, a large internet infrastructure provider, said in an email that the Mirai bot count (the number of infected devices that can be used to launch attacks) is as high as 500,000 as of this week, and added that “it’s possible” that someone could rent the “full power of the bot.”
It’s possible that the two have found a way to reach an almost-monopoly over other Mirai botnets by scanning for new targets using a recently disclosed flaw, and by being faster at infecting and re-infecting targets, according to security researchers. (Usually devices infected by Mirai can remove the malware simply by rebooting, but they can then be reinfected by Mirai or other malware again).
“The simplest way is just being faster than everyone else [...] when a device becomes uninfected, it’s a ‘race.’”
The two hackers for now seems to be winning this race, which might be bad news for the internet. BestBuy, however, claim the two have ethical limits, blacklisting certain IPs to prevent their customers from hitting “critical infrastructure of specific companies.”
“Business is business but there is limit to everything. Some things in the internet you should not hit.”
Tomi Engdahl says:
DDoS script kiddies are also… actual kiddies, Europol arrests reveal
Young ‘uns hire tools to hit infrastructure, info systems
http://www.theregister.co.uk/2016/12/12/europol_arrests_34_ddos_kiddies/
Law enforcement bods at Europol have arrested 34 users of Distributed Denial of Service (DDoS) cyber-attack tools and interviewed and cautioned 101 suspects in a global crackdown.
Unsurprisingly, the users identified by Europol’s European Cybercrime Centre (EC3) were mainly young adults under the age of 20.
The body worked with regional agencies to identify cyber-attackers that had targeted critical infrastructure and information systems in the European Union.
The individuals arrested are suspected of paying for stressers and booters services to maliciously deploy software to launch DDoS attacks.
The tools used are part of the criminal “DDoS for hire” facilities for which hackers can pay and aim at targets of their choosing, said Europol in its press release.
“Today’s generation is closer to technology than ever before, with the potential of exacerbating the threat of cybercrime. Many IT enthusiasts get involved in seemingly low-level fringe cybercrime activities from a young age, unaware of the consequences that such crimes carry.”
Europol is currently conducting a prevention campaign in all participating countries in order to raise awareness of the risk of young adults getting involved in cybercrime.
Tomi Engdahl says:
Here are some best practices for preventing DDoS attacks
Preventing Distributed Denial of Service attacks is both a technical and business issue.
http://www.zdnet.com/article/here-are-some-best-practices-for-preventing-ddos-attacks/
Distributed denial-of-service (DDoS) made lots of headlines in late October when a massive DDoS attack on Domain Name System (DNS) service provider Dyn temporarily disrupted some of the most popular sites on the internet.
DDoS attacks are clearly on the rise. A report by content delivery network provider Akamai earlier this year said such incidents are increasing in number, severity and duration. It noted a 125 percent increase in DDoS attacks year over year and a 35 percent jump in the average attack duration.
When the Software Engineering Institute (SEI) at Carnegie Mellon University recently posted a blog titled, “Distributed Denial of Service Attacks: Four Best Practices for Prevention and Response,” it became SEI’s most visited post of the year after only two days, according to a spokesman for the institute.
Distributed Denial of Service Attacks: Four Best Practices for Prevention and Response
https://insights.sei.cmu.edu/sei_blog/2016/11/distributed-denial-of-service-attacks-four-best-practices-for-prevention-and-response.html
Architecture. To fortify resources against a DDoS attack, it is important to make the architecture as resilient as possible.
The following steps will help disperse organizational assets as to avoid presenting a single rich target to an attacker:
Locate servers in different data centers.
Ensure that data centers are located on different networks.
Ensure that data centers have diverse paths.
Ensure that the data centers, or the networks that the data centers are connected to, have no notable bottlenecks or single points of failure.
Hardware. Deploy appropriate hardware that can handle known attack types and use the options that are in the hardware that would protect network resources. Again, while bolstering resources will not prevent a DDoS attack from happening, doing so will lessen the impact of an attack.
In particular, certain types of DDoS attacks have been in existence for quite some time, and a lot of network and security hardware is capable of mitigating them. For example, many commercially available network firewalls, web application firewalls, and load balancers can defend against layer 4 attacks
Bandwidth. If affordable, scale up network bandwidth. For volumetric attacks, the solution some organizations have adopted is simply to scale bandwidth up to be able to absorb a large volume of traffic if necessary.
Outsourcing. There are several large providers that specialize in scaling infrastructure to respond to attacks. These providers can implement cloud scrubbing services for attack traffic to remove the majority of the problematic traffic before it ever hits a victim’s network.
An ISP can offer DDoS mitigation services that will help organizations respond in the wake of an attack.
Tomi Engdahl says:
Dozens of Teens Arrested Over DDoS Attacks
http://www.securityweek.com/dozens-teens-arrested-over-ddos-attacks
Europol on Monday announced that 34 arrests were made as part of an operation targeting users of Distributed Denial of Service (DDoS) cyber-attack tools.
The operation was conducted between December 5 and 9, 2016, and received cooperation from law enforcement agencies all around the world, including Australia, Belgium, France, Hungary, Lithuania, the Netherlands, Norway, Portugal, Romania, Spain, Sweden, the United Kingdom and the United States. In addition to the 34 arrests, 101 suspects were interviewed and cautioned, Europol says.
The agency believes that the arrested individuals were paying for stressers and booters services to maliciously deploy software to launch DDoS attacks. The attacks flooded web servers with massive amounts of data, thus rendering them inaccessible to users.
Tomi Engdahl says:
14,000 Domains Dropped Dyn’s DNS Service After Mirai Attack
https://it.slashdot.org/story/17/02/05/2046224/14000-domains-dropped-dyns-dns-service-after-mirai-attack
New data suggests that some 14,500 web domains stopped using Dyn’s Managed DNS service in the immediate aftermath of an October DDoS attack by the Mirai botnet. That’s around 8% of the web domains using Dyn Managed DNS… “The data show that Dyn lost a pretty big chunk of their customer base because they were affected by (Mirai),”
Exclusive: Mirai Attack Was Costly For Dyn, Data Suggests
https://securityledger.com/2017/02/mirai-attack-was-costly-for-dyn-data-suggests/
In-brief: More than 14,000 Internet domains stopped using managed DNS services from Dyn, the New Hampshire based company, following an October botnet attack on the company, data from Bitsight suggests.
The Mirai botnet attacks that took managed Domain Name System services from New Hampshire based Dyn offline in October caused short-lived pain for Internet users trying to reach popular web sites like PayPal, Twitter, Reddit, Amazon, Netflix, and Spotify.
The attacks may have had more lasting implications for Dyn – and other Internet companies like it- as new data suggests that around 8% of the web domains relying on Dyn’s managed DNS service dropped the service in the immediate aftermath of the attack.
“The data show that Dyn lost a pretty big chunk of their customer base because they were affected by (Mirai),”
Dyn was one of a handful of organizations that were the victim of a series of distributed denial-of-service (DDoS) attacks starting on October 21st. The attacks were launched by a global population of Internet of Things devices like IP enabled cameras and digital video recorders (DVRs) that had been infected with malicious software known as “Mirai.”
Following the attack, 139,000 of the 145,000 domains continued to use Dyn exclusively, a loss of 6,000 domains or around 4% of the total.
The impact of the botnet attack would have hit companies that exclusively used Dyn’s services the most severely, preventing Internet users who were trying to reach those web sites, hosted web applications and other services from doing so. But the public facing outages may have only been a small part of the total impact, Dahlberg said. Companies using DYN for API (application program interface) or software updates would have been affected in many ways – not just web site availability, he said.
It is unclear whether some of the 14,500 domains that dropped Dyn’s services in the immediate aftermath of the botnet attack may have returned to Dyn.