How to hack to an embedded device? On-chip debug (OCD) interfaces can provide chip-level control of a target device and are a primary vector used by engineers, researchers, and hackers to extract program code or data, modify memory contents, or affect device operation on-the-fly. Depending on the complexity of the target device, manually locating available OCD connections can be a difficult and time consuming task.
Hackaday posting DEF CON: Tamper Evidence, Contests, and Embedded Talks pointed to an interesting looking hardware JTAGulator.
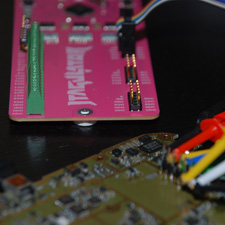
JTAGulator is an open source hardware tool that assists in identifying OCD connections from test points, vias, or component pads on a target device. It gives 24 I/O channels (adjustable from 1.2V to 3.3V levels) with input protection circuitry. Supported target interfaces are JTAG/IEEE 1149.1 and UART/asynchronous serial. The device connects to host computer through USB.
I have not tested this device, but this looks interesting.
7 Comments
Tomi Engdahl says:
JTAGulator Finds Debug Interfaces
http://hackaday.com/2013/10/02/jtagulator-finds-debug-interfaces/
[Joe Grand] has come up with a tool which we think will be useful to anyone trying to hack a physical device: The JTAGulator. We touched on the JTAGulator briefly during our DEF CON coverage, but it really deserves a more in-depth feature. The JTAGulator is a way to discover On Chip Debug (OCD) interfaces on unfamiliar hardware.
Open any cell phone, router, or just about any moderately complex device today, and you’ll find test points. Quite often at least a few of these test points are the common JTAG / IEEE 1149.1 interface.
JTAG interfaces have 5 basic pins: TDI (Test Data In), TDO (Test Data Out), TCK (Test Clock), and TMS (Test Mode Select), /TRST (Test Reset) (optional).
If you’re looking at a PCB with many test points, which ones are the JTAG pins? Also which test points are which signals?
The idea is simple: Connect the JTAGulator to the test points on the PCB under test, issue a few commands via a serial terminal, and let the JTAGulator do the rest. It performs a brute force approach on every permutation of pins, issuing basic JTAG commands – either IDCODE or BYPASS, and looking for a response. If any valid responses are received, the JTAGulator displays the found interface’s pinout.
Tomi Engdahl says:
JTAGulator
http://www.grandideastudio.com/portfolio/jtagulator/
JTAGulator is an open source hardware tool that assists in identifying OCD connections from test points, vias, or component pads on a target device.
Assembled JTAGulators are available from Parallax, Inc.
JTAGulator $159.99
http://parallax.com/product/32115
Tomi Engdahl says:
Given an Arduino compatible microcontroller JTAGenum scans pins[] for basic JTAG functionality and can be used to enumerate the IR for undocumented opcodes.
https://github.com/cyphunk/JTAGenum/
Tomi Engdahl says:
A Hacker’s Guide To JTAG
https://hackaday.com/2020/04/08/a-hackers-guide-to-jtag/
Tomi Engdahl says:
https://hackaday.com/2023/08/11/using-jtag-to-dump-the-xboxs-secret-boot-rom/
Tomi Engdahl says:
https://hackaday.com/2024/05/12/jtag-hacking-an-ssd-with-a-pi-a-primer/
Tomi Engdahl says:
https://blog.samtec.com/post/what-is-a-jtag-connector/