Taking a Trip to the ATM? Beware of ‘Skimmers’. Skimming is the theft of credit card information used in an otherwise legitimate transaction. Instances of skimming have been reported where the perpetrator has put a device over the card slot of an ATM (automated teller machine), which reads the magnetic strip as the user unknowingly passes their card through it. Technology needed to read the contents of the magnetic strip is pretty simple.
The Evolution of ATM Skimmers article tells that in a little over a decade, ATM skimmers have gone from urban myth to a wildly complex, ever-evolving suite of technologies that has the potential to be the worst nightmare of anyone with a bank account. The Evolution of ATM Skimmers article look at how quickly skimmers have evolved—and why they’re increasingly impossible to spot.
Check also FBI article on skimming and my earlier postings on credit card security and banking security.

18 Comments
Tomi Engdahl says:
Fuel Station Skimmers: Primed at the Pump
http://krebsonsecurity.com/2015/02/fuel-station-skimmers-primed-at-the-pump/
notice the pump and credit card reader festooned with security tape that conjures up images of police tape around a crime scene.
The tape carries the bold yet misguided assurance, “securing your identity.”
The tape on the reader is intended to protect against pump reader skimmers, like the one pictured below, which sells in underground forums for upwards of USD $2,000 and is designed to be fit directly over top of the readers they have at many ESSO/Exxon fuel pumps.
Of course, security tape wrapped around a card reader at a gas pump isn’t going to stop most pump skimming attacks
The crooks figured out a long time ago that only a handful of master keys are needed to open the majority of the gas pumps in use today. So, rather than retrofit each one of these pumps with a more custom and secure locking mechanism, most stations just put security tape on the pump door.
I don’t worry too much about gas pump skimmers; I always use my credit card, and know that I am not liable for unauthorized charges on my card as long as I report it to my bank or credit card company.
Tomi Engdahl says:
Hacking ATMs, Literally
http://krebsonsecurity.com/2015/04/hacking-atms-literally/
Most of the ATM skimming attacks written about on this blog conclude with security personnel intervening before the thieves manage to recover their skimmers along with the stolen card data and PINs. However, an increasingly common form of ATM fraud — physical destruction — costs banks plenty, even when crooks walk away with nothing but bruised egos and sore limbs.
An ATM technician and KrebsOnSecurity reader shared photos of a recent attack in which three would-be robbers went to town on a wall-mounted cash machine with crowbars and hammers.
Comment:
To rob an ATM a hacker needs a laptop and sledge hammer. Sledge hammer is necessary to break an ATM to pull out money. Why a laptop is needed you may ask? Every hacker needs a laptop in other case he isn’t a hacker.
Tomi Engdahl says:
Reverse Engineering An ATM Card Skimmer
http://hackaday.com/2016/05/03/reverse-engineering-an-atm-card-skimmer/
While vacationing in Bali, [Matt South] walked into a nice, secure, air-conditioned cubicle housing an ATM. Knowing card skimmers are the bane of every traveller, [Matt] did the sensible thing and jiggled the card reader and the guard that hides your PIN when punching it into the numeric keypad. [Matt] found the PIN pad shield came off very easily and was soon the rightful owner of a block of injection molded plastic, a tiny camera, and a few bits of electronics.
The first thing that tipped [Matt] off to the existence of electronics in this brick of plastic was a single switch and a port with four contacts.
Can’t Hack a Hacker: Reverse Engineering a Discovered ATM Skimmer
https://trustfoundry.net/reverse-engineering-a-discovered-atm-skimmer/
Brian Krebs has produced numerous articles on ATM skimmers. He has essentially become the “go to” journalist on ATM fraud. From reading his stuff, I have learned how the “bad guys” think when it comes to ATM fraud. In a nutshell, they are after two things:
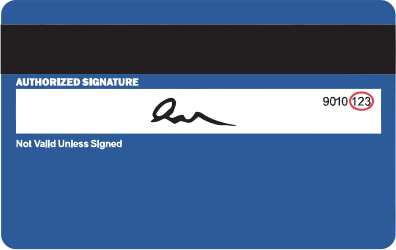
1. They want your card number
2. They want your PIN number
To get your card number, the thieves have a few options. Traditionally, they affix a device to the ATM card reader that “skims” your card as it passes into the actual machine.
ATM skimmer that sits in front of the card reader
The devices must look as close to the actual reader as possible so they don’t arouse suspicion. The blackhats go to great lengths to achieve this.
Krebs recommends two simple protections.
Jiggle that ATM
1. Give the card reader area a good yank. Don’t get out your crowbar, just see if any pieces of the ATM come-off easily. Usually the skimmers will snap into place or use light adhesive so they can be easily removed and swapped-out by the thieves.
2. Cover your PIN with your hand
This will not protect you from PIN overlays, but it will hide your PIN from hidden cameras. Plus it’s so easy to do, why wouldn’t you?
By the time we got to the restaurant, we were pretty scared, A GSM-enabled device could feasibly phone home with its GPS coordinates. Just in case, we asked for some aluminum foil and made a makeshift Faraday cage. When it comes to Indonesian criminal gangs, you can never be too careful.
I had to hold the wires in with my hand while I plugged the USB cable into my computer. I crossed my fingers and….
It mounts! I freak-out a little and begin copying the files from the device. There are two folders. One is named “Google Drive” and one is named “VIDEO”.
Some other interesting footage include the skimmer being installed.
On the left you see the power source [Samsung battery], the controller board is on the right with some ribbon cable that goes up to the pinhole camera.
Googling the number from the controller board revealed that it is a commercially available board used in spy camera gear.
The overall design choices of the skimmer were actually pretty decent.
The device is handmade not mass-produced.
I never found a physical card skimmer (the part of the system that grabs the card number). The wires visible behind the machine make me think the card numbers are probably being skimmed over the network.
Tomi Engdahl says:
Gas Pump Skimmers
https://learn.sparkfun.com/tutorials/gas-pump-skimmers
This is the not the first or the second time SparkFun has dealt with credit card skimmers. The difference is that this time the local governmental agency politely asked for help and we’re always down for trying to put a stop to bad actors.
We were given three skimmers found installed within gas pumps with the request that we try to get the data off the board so that the agents could let those who’ve had their credit card compromised know so they can get a new card. Not great, but it’s a start. Second task: can we build a jig or system so that they can more easily poke at these systems in the future.
Tomi Engdahl says:
Seriously, Is It That Easy To Skim Cards?
https://hackaday.com/2017/09/20/seriously-is-it-that-easy-to-skim-cards/
The folks at Sparkfun write about an approach they received from a law enforcement agency bearing a selection of card skimmer devices that had been installed in gasoline pumps. These didn’t rely on interception of the card itself, instead they sat as a man-in-the-middle attack in the serial line between the card reader unit and the pump electronics. Let that sink in for a minute: a serial line that is readily accessible to anyone with the pump manufacturer’s standard key, carries card data in an unencrypted form. The owner of the skimming device is the criminal, but the company leaving such a wide-open vulnerability should really be joining them in having to answer to authorities.
Gas Pump Skimmers
https://learn.sparkfun.com/tutorials/gas-pump-skimmers
Tomi Engdahl says:
Someone finally made an app to detect credit card skimmers at the gas pump
https://thenextweb.com/apps/2017/09/20/heres-how-to-stop-criminals-from-stealing-your-credit-card-info-at-the-gas-pump/#.tnw_LM3TBBkI
In less than 30 seconds a hacker can install a $10 piece of pre-built hardware – easily purchased online – into a gas pump. This device is called a skimmer and it’s designed to get your credit card number when you use it at the pump.
A clever developer came up with a somewhat simple approach to protecting yourself at the gas station. The CEO and Founder of SparkFun, Nate Seidle, along with programmer Nick Poole, built a free, open-source Android app to detect popular skimmers.
The app detects a specific Bluetooth signal and, if found, it tries to establish a connection and send a command that will verify the existence of a skimmer in your general area. The app is looking for Bluetooth networks with an ID of HC-05, which turned out to be the default on devices Seidle tested; if it finds one you’ll be alerted.
SparkFun’s Bluetooth device-detecting app is called Skimmer Scanner and it’s a bare-bones tool that appears to work as intended. It’s free and open-source and the developer says it doesn’t keep or record any information.
https://play.google.com/store/apps/details?id=skimmerscammer.skimmerscammer&hl=en&rdid=skimmerscammer.skimmerscammer
Tomi Engdahl says:
Seek Out Scammers With Skimmer Scanner
https://hackaday.com/2017/09/25/seek-out-scammers-with-skimmer-scanner/
Last week we reported on some work that Sparkfun had done in reverse engineering a type of hardware card skimmer found installed in gasoline pumps incorporating card payment hardware. The device in question was a man-in-the-middle attack, a PIC microcontroller programmed to listen to the serial communications between card reader and pump computer, and then store the result in an EEPROM.
The devices featured a Bluetooth module through which the crooks could harvest the card details remotely, and this in turn provides a handy way to identify them in the wild. If you find a Bluetooth connection at the pump bearing the right identification and with the right password, it can then be fingered as a skimmer by a simple response test. And to make that extra-easy they had written an app, which when we reported on it was available from a GitHub repository.
In a public-spirited move, they are now calling upon the hardware hacker and maker community to come together today, Monday, September 25th, and draw as much attention as possible to these devices in the wild, and with luck to get a few shut down. To that end, they have put a compiled version of the app in the Google Play Store to make it extra-easy to install on your phone, and they are asking for your help.
https://play.google.com/store/apps/details?id=skimmerscammer.skimmerscammer
Tomi Engdahl says:
https://krebsonsecurity.com/2019/11/hidden-cam-above-bluetooth-pump-skimmer/
Tomi Engdahl says:
Gas Pump Skimmers
https://learn.sparkfun.com/tutorials/gas-pump-skimmers
Tomi Engdahl says:
Undetectable ATM “Shimmers” Hacker’s Latest Tool for Steal your Chip Based Card Details from POS Terminal
https://gbhackers.com/undetectable-atm-shimmers-hackers-latest-tool-for-steal-your-chip-based-card-details/
Latest warning coming out from Canada about sophisticated ATM skimming called “Shimmers” targeted chip-based credit and Debit cards to steal your entire card information form POS(Point-of-sale) terminal.
Basically many skimming devices record your card information in plain text on the magnetic stripe on the backs of cards.
Last Year November ATM based Skimmer has been detected a threat on ATM fraud devices known as “insert skimmers,”these thin data theft tools made to be completely hidden inside of a cash’s machine’s card acceptance slot.
Shimmers have rendered the bigger and bulkier skimmers virtually obsolete,
” A shimmer, on the other hand, is so named because it acts a shim that sits between the chip on the card and the chip reader in the ATM — recording the data on the chip as it is read by the ATM.”
ATM giant NCR Corp wrote in a 2016 alert ,The only way for this attack to be successful is if a [bank card] issuer neglects to check the CVV when authorizing a transaction.
Customers using the tap function of a chip card is one way to avoid being “shimmed.”It’s actually very secure. Each tap transfers very limited banking information, which can’t be used to clone your card.
Tomi Engdahl says:
Gas Pump Skimmers
https://learn.sparkfun.com/tutorials/gas-pump-skimmers/all
What’s the first thing that should scare you? There’s three. And the next? The label ‘46’. They’ve got so many in the field criminals need to number them just to keep track.
Tomi Engdahl says:
The new card skimming is called ‘shimming’
It targets EMV chip cards and is hard to detect, but remains rare
https://www.creditcards.com/credit-card-news/new-card-skimming-is-called-shimming.php
Tomi Engdahl says:
Credit card terminal extreme teardown
https://www.youtube.com/watch?v=n9zPq4_Evvw
A lot of the anti-tampering techniques in this were also used by arcade game companies to stop people from reading the game data off the boards.
Tomi Engdahl says:
Review of the Hunter Cat Portable Credit Card Skimmer Detector
https://blog.hackster.io/review-of-the-hunter-cat-portable-credit-card-skimmer-detector-3be7199ddfa4
Tomi Engdahl says:
Detecting Credit Card Skimmers
https://www.schneier.com/blog/archives/2019/08/detecting_credi_1.html
Modern credit card skimmers hidden in self-service gas pumps communicate via Bluetooth.
Tomi Engdahl says:
https://hackaday.com/2019/11/15/credit-card-skimmers-evolve-shimmers-are-here/
Tomi Engdahl says:
Watch a Card Skimmer Get Installed in Seconds
BY MATTHEW HUMPHRIES 13 FEB 2018, 3:51 P.M.
Overlay skimmers simply stick on top of card readers and can be installed even in busy supermarket checkout lanes.
https://uk.pcmag.com/news-analysis/93337/watch-a-card-skimmer-get-installed-in-seconds
Tomi Engdahl says:
Protect Your Credit Card By Building a Skimmer Detector with a Raspberry Pi
https://www.hackster.io/news/protect-your-credit-card-by-building-a-skimmer-detector-with-a-raspberry-pi-f670f94ffcb2
Credit card skimmers are so effective because they’re very simple. Usually, they’re small modules that are connected to the magnetic stripe…