https://blog.github.com/2018-03-14-eu-proposal-upload-filters-code/
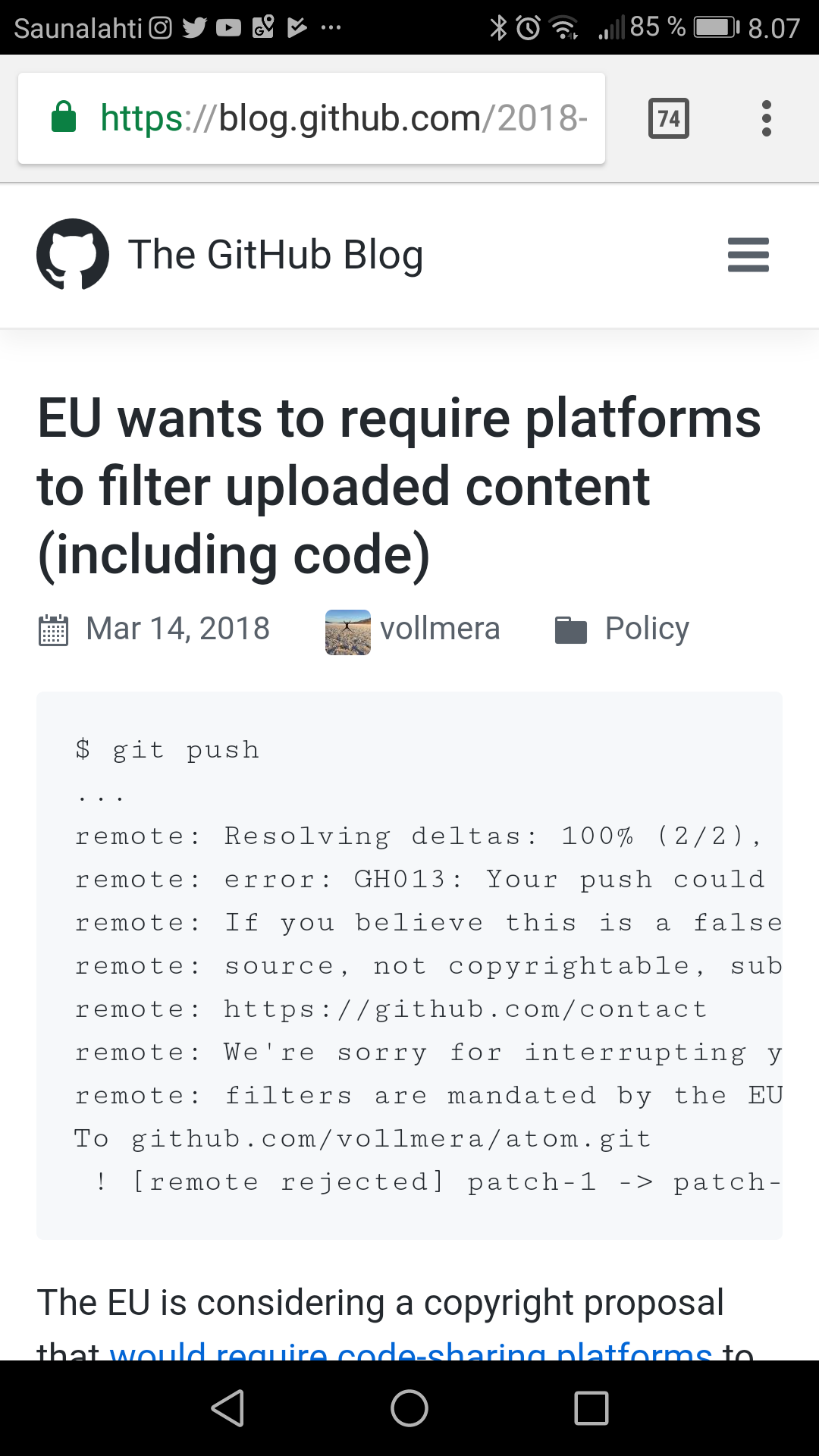
The EU is considering a copyright proposal that would require code-sharing platforms to monitor all content that users upload for potential copyright infringement (see the EU Commission’s proposed Article 13 of the Copyright Directive). The proposal is aimed at music and videos on streaming platforms. However, the way it’s written captures many other types of content, including code.
Upload filters (“censorship machines”) are one of the most controversial elements of the copyright proposal, raising a number of concerns.
 SAVE CODE SHARE letter urges to take action:
SAVE CODE SHARE letter urges to take action:
Current EU Copyright Reviewthreatens Free and Open Source Software. Take action now to preserve the ability to collaboratively build software online!

3 Comments
Tomi Engdahl says:
Tell MEPs now “Vote no to the link tax and to automated censorship filters.”
https://savethelink.org/me
Tomi Engdahl says:
GitHub Security Alerts Lead to Fewer Vulnerable Code Libraries
https://www.securityweek.com/github-security-alerts-lead-fewer-vulnerable-code-libraries
GitHub says the introduction of security alerts last year has led to a significantly smaller number of vulnerable code libraries on the platform.
The code hosting service announced in mid-November 2017 the introduction of a new security feature designed to warn developers if the software libraries used by their projects contain any known vulnerabilities.
The new feature looks for vulnerable Ruby gems and JavaScript NPM packages based on MITRE’s Common Vulnerabilities and Exposures (CVE) list. When a new flaw is added to this list, all repositories that use the affected version are identified and their maintainers informed. Users can choose to be notified via the GitHub user interface or via email.
When it introduced security alerts, GitHub compared the list of vulnerable libraries to the Dependency Graph in all public code repositories.
The Dependency Graph is a feature in the Insights section of GitHub that lists the libraries used by a project. Since the introduction of security alerts, this section also informs users about vulnerable dependencies, including CVE identifiers and severity of the flaws, and provides advice on how to address the issues.
Tomi Engdahl says:
http://www.epanorama.net/newepa/2018/09/11/julia-reda-showdown-on-upload-filters-and-the-link-tax-on-september-12-these-are-the-options-in-front-of-meps/