I wrote a technical article on embedded systems and IoT security to Uusiteknologia.fi magazine:
Designing modern electronics+ information security
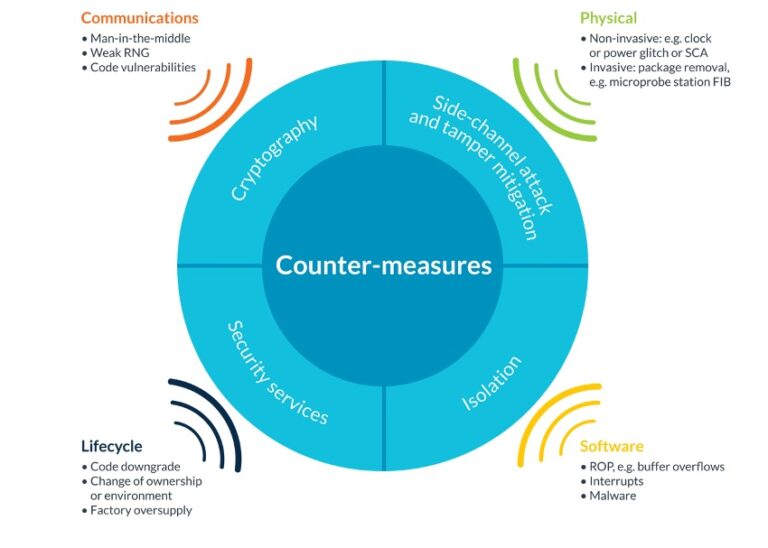
With the latest smart electronics and embedded microprocessors, devices connected to the network can be implemented even better, but even better care must be taken of their data security and protections.
This Designing modern electronics article gives information for the information security protection of modern electronics. Embedded systems are prone to various information security risks, which in the worst case can cause serious consequences for both users and the environment.
That is why information security should be taken into account from the outset, from the design phase of the device or system to the maintenance phase and decommissioning at the end of the solution’s life cycle.
An insecure Internet of Things can pose a significant risk to the entire digital operating environment. And since the Internet is already ubiquitous, every IoT device is vulnerable to attack.
Although the goal should always be to achieve sustainable security, information security operations must be functional already when the product leaves the factory and must be maintained with software updates.
Designers of embedded systems must adopt a security-first approach to ensure that the systems they design are protected from security risks. Therefore, network security, software security and physical security are important in IoT devices.
This article has provided a basic understanding of information security in embedded systems and provides a guide for designers to create reliable and secure systems that are safe for both users and the environment.
Here you can my article in Finnish:
Nykyelektroniikan suunnittelukoulu Plus, osa 5: Sulautettujen ja IoT-ratkaisujen tietoturva
https://www.uusiteknologia.fi/2023/11/08/nykyelektroniikan-suunnittelukoulu-plus-osa-5-sulautettujen-ja-iotn-tietoturva/
If you want to get idea of the article content in English, try Google translation of the article.
66 Comments
Tomi Engdahl says:
Update devices remotely with this open source tool
Handle all your complete device updates, including firmware and bootloaders, over the air with UpdateHub Community Edition.
https://opensource.com/article/20/9/update-remote-devices-updatehub
Tomi Engdahl says:
https://www.redhat.com/en/blog/linux-security-aide
Tomi Engdahl says:
https://www.reddit.com/r/linuxquestions/comments/1bixls9/does_linux_have_any_mechanisms_for_verifying/
Tomi Engdahl says:
https://exeon.com/knowledge/cvss/?utm_term=cvss%20vulnerability&utm_campaign=R+%7C+CVSS+%7C+EN+%7C+Search&utm_source=adwords&utm_medium=ppc&hsa_acc=5926591164&hsa_cam=21422420589&hsa_grp=164841426435&hsa_ad=704498221670&hsa_src=g&hsa_tgt=kwd-808277578273&hsa_kw=cvss%20vulnerability&hsa_mt=p&hsa_net=adwords&hsa_ver=3&gad_source=1&gad_campaignid=21422420589&gclid=EAIaIQobChMI5vao5_7KjwMVbBiiAx0j5TSbEAAYAiAAEgJTwPD_BwE
Tomi Engdahl says:
https://phoenixnap.com/kb/nmap-scan-open-ports
Tomi Engdahl says:
https://veracrypt.io/en/Downloads.html
Tomi Engdahl says:
How many programmers does it take to screw in a light bulb?
None, that’s a hardware problem.
How many hackers does it take to screw up an IoT controlled light bulb?
That’s everybody’s problem.
Tomi Engdahl says:
You know you are poor when an AWS outage doesn’t affect you because you can still easily use your bed, kitchen appliances to make a cup of tea or joe (or heat food), use the toilet, and open any door in your home. See? Being poor is not so bad. Lmao.
yes it is real https://www.cnet.com/health/sleep/owners-of-luxury-smart-beds-literally-lost-sleep-due-to-aws-outage/
Tomi Engdahl says:
Functional story when IoT fails:
The Silent Winter – When Berlin’s Heating Systems Failed
https://www.linkedin.com/pulse/silent-winter-when-berlins-heating-systems-failed-kattwinkel-t2hye?utm_source=share&utm_medium=member_android&utm_campaign=share_via
Tomi Engdahl says:
Manufacturer issues remote kill command to disable smart vacuum after engineer blocks it from collecting data — user revives it with custom hardware and Python scripts to run offline
News
By Jowi Morales published November 1, 2025
The smart vacuum cleaner was remotely bricked for not collecting data.
https://www.tomshardware.com/tech-industry/big-tech/manufacturer-issues-remote-kill-command-to-nuke-smart-vacuum-after-engineer-blocks-it-from-collecting-data-user-revives-it-with-custom-hardware-and-python-scripts-to-run-offline
Tomi Engdahl says:
IEC-standardi auttaa teollisuuden NIS2-vaateita
https://www.uusiteknologia.fi/2025/11/18/iec-standardi-auttaa-teollisuuden-nis2-vaateita/
Euroopan unionin uuden NIS2-direktiivin velvoitteet tulivat Suomessa voimaan kuluvan vuoden keväänä. Jatkossa teollisuuden kriittisten alojen toimijoilta edellytetään entistä parempaa verkko- ja tietoturvan tasoa sekä tarkkoja raportointikäytäntöjä. Niihin päästään helpoiten esimerkiksi IEC-standardisoinnin avulla.
Kyberhyökkäykset ovat nykyään vakava uhka yrityksille ja organisaatioille toimialasta riippumatta. Euroopan unionin NIS2-direktiivin myötä muun muassa kemianteollisuus, elintarviketuotanto ja monet valmistavan teollisuuden toimijat siirtyivät tarkemman seurannan piiriin.
Schneider Electricin Umberto Cattaneo suosittelee teollisuusyrityksiä tukeutumaan valmiisiin standardeihin, joita noudattamalla on helppoa nostaa oma OT-kyberturvallisuus direktiivin vaatimalle tasolle.
Suomessa NIS2-direktiivi on jo otettu osaksi paikallista lainsäädäntöä, ja Traficom valvoo siihen liittyvää raportointia. NIS2 asettaa kyberturvallisuudelle uuden perusvaatimustason, joka vastaa paremmin moderneihin kyberuhkiin. Aiemman NIS-direktiivin piirissä olleilta toimijoilta esimerkiksi energia-alalla, liikenteessä ja vesihuollossa edellytetään entistä tarkempaa kyberturvan riskienhallintaa, suojautumista, raportointia ja dokumentointia.
Uusi direktiivi velvoittaa keskeisiksi ja tärkeiksi määriteltyjä toimijoita osoittamaan, että ne noudattavat NIS2-vaatimuksia. Perusta rakennetaan hyväksytyn ja dokumentoidun kyberturvallisuusstrategian ja riskienhallintaprosessin päälle. Toimijoilla tulee olla myös valmiit prosessit kyberhyökkäyksistä raportointiin sekä teknistä näyttöä ja dokumentointia siitä, että niiden toiminta on hyväksyttävällä tasolla.
Schneider Electricin Umberto Cattaneo kannustaa toimijoita hyödyntämään olemassa olevia standardeja, joiden avulla on helppoa todistaa kyberturvallisuuden olevan kunnossa. Teollisuuden alalla hyvä lähtökohta on IEC 62443 -standardisarja, jossa määritellään automaation ja ohjausjärjestelmien kyberturvallisuuden hallintamallit, tekniset kontrollit ja riskienhallinnan prosessit.
IEC 62443 -standardi koskee sekä informaatioteknologiaa (IT) että operatiivista teknologiaa (OT). Ennen OT-järjestelmien toiminta oli eriytettyä, mutta raja IT- ja OT-järjestelmien välillä on hämärtynyt huomattavasti viime vuosina. Siksi myös OT-ympäristöjen asianmukainen suojaaminen on entistä tärkeämpää teollisuudessa.
Tomi Engdahl says:
https://etn.fi/index.php/13-news/18321-kyberturva-tulee-seuraavaksi-moottoripyoeriin
Tomi Engdahl says:
Lääkintälaitteiden internet (IoMT) yhdistää diagnostiikan, puettavat anturit ja sairaalalaitteet pilvipohjaisiin järjestelmiin.
Tomi Engdahl says:
https://etn.fi/index.php/13-news/18680-nordic-tuo-iot-laitteille-elinkaaren-mittaisen-paeivitysinfran-kertamaksulla
Tomi Engdahl says:
https://www.uusiteknologia.fi/2025/11/18/iec-standardi-auttaa-teollisuuden-nis2-vaateita/
Tomi Engdahl says:
Sulautetut järjestelmät saivat vihdoin oman kyberuhkamallinsa
https://etn.fi/index.php/13-news/18460-sulautetut-jaerjestelmaet-saivat-vihdoin-oman-kyberuhkamallinsa
Sulautettujen järjestelmien tietoturva ottaa merkittävän askeleen eteenpäin. MITRE on julkaissut uuden kyberturvakehyksen nimeltä Embedded Systems Threat Matrix (ESTM).
ESTM on sulautetuille järjestelmille tehty uhkamalli. Se on ATT&CK-kehyksen vastine laitteille, firmwarelle ja rautaläheisille ympäristöille. Aiemmin embedded-järjestelmien uhkia on jouduttu mallintamaan IT- ja pilviympäristöihin tarkoitetuilla työkaluilla.
Uusi malli kuvaa järjestelmällisesti hyökkäystavat, jotka kohdistuvat esimerkiksi käynnistysketjuun, firmware-päivityksiin, debug-rajapintoihin, väyliin ja fyysiseen pääsyyn laitteeseen. Mukana ovat myös supply chain -uhat.
MITRE on kehittänyt ESTM:n yhteistyössä Yhdysvaltain ilmavoimien CROWS-ohjelman kanssa. Taustalla ovat puolustusjärjestelmät ja kriittinen infrastruktuuri, kuten energia, liikenne, terveydenhuolto ja teollisuusautomaatio.
Kyse ei ole kokeellisesta mallista. Nyt julkaistu versio on ESTM 3.0, eli kehys on jo kypsynyt käytännön käyttöön. Se toimii yhdessä MITREn EMB3D-uhkamallin kanssa ja tukee koko järjestelmän elinkaaren aikaista turvallisuussuunnittelua.
Käytännössä ESTM tarjoaa yhteisen kielen laitevalmistajille, tietoturva-asiantuntijoille ja viranomaisille. Sillä voidaan tehdä uhkamallinnusta, analysoida hyökkäyspolkuja ja määritellä turvallisuusvaatimuksia jo suunnitteluvaiheessa.