Row hammer (also written as rowhammer) is a security exploit that takes advantage of an unintended and undesirable side effect in dynamic random-access memory (DRAM) in which memory cells interact electrically between themselves by leaking their charges, possibly changing the contents of nearby memory rows that were not addressed in the original memory access. The initial research into the row hammer effect, published in June 2014. Rowhammer attacks work by accessing—or hammering—physical rows inside vulnerable chips millions of times per second in ways that cause bits in neighboring rows to flip, meaning 1s turn to 0s and vice versa.
Rowhammer is a vulnerability caused by leaking charges in DRAM cells that enables attackers to induce bit flips in DRAM memory. The Rowhammer issue, which has been around for over one decade, exists because cells on DRAM chips are smaller and closer to each other, making it difficult to prevent electrical interaction between them. Thus, by repeatedly accessing data in a row of memory, data in nearby rows may become corrupted.
Different methods have been developed for more or less successful detection, prevention, correction or mitigation of the row hammer effect. And more attacks as well. To stop Rowhammer, DRAM implements a mitigation known as Target Row Refresh (TRR). ECC cannot provide complete protection against Rowhammer but makes exploitation harder.
In 2016 it was shown that Rowhammer bitflips can be used to root Android phones.
RAMBleed published on 2019 is a side-channel attack that enables an attacker to read out physical memory belonging to other processes. The implications of violating arbitrary privilege boundaries are numerous.
Researchers have shown the attacks can be used to give untrusted applications nearly unfettered system privileges, bypass security sandboxes designed to keep malicious code from accessing sensitive operating system resources, and root or infect Android devices, among other things.
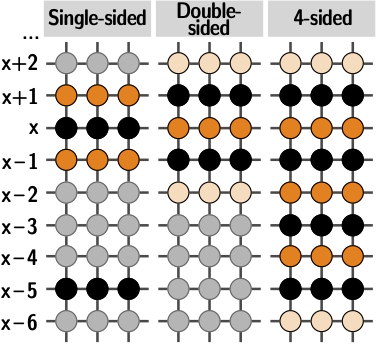
Now there are new findings. The new attack is called Blacksmith. Researchers say they used a new Rowhammer exploit to successfully flip bits on all 40 PC-DDR4 DRAM devices they tested, defeating recent hardware mitigations. Researchers build “fuzzer” that supercharges potentially serious bitflipping exploits: Rowhammer exploits that allow unprivileged attackers to change or corrupt data stored in vulnerable memory chips are now possible on virtually all DDR4 modules due to a new approach that neuters defenses chip manufacturers added to make their wares more resistant to such attacks. The researchers conducted experiments on 40 DDR4 DIMMs (from Samsung, Micron, and SK Hynix) to explore the possibility of bypassing mitigations through “accessing aggressor rows in non-uniform access patterns.” They did not find any DIMMs that are completely safe. Some DIMMs are more vulnerable to this new Rowhammer patterns than others.
Blacksmith Rowhammer Fuzzer Bypasses Existing Protections. Blacksmith attack demonstrates that DDR4 memory protections are broken wide open by new Rowhammer technique. The researchers used non-uniform patterns that access two or more aggressor rows with different frequencies. The result: all 40 of the randomly selected DIMMs in a test pool experienced bitflips, up from 13 out of 42 chips tested in previous work from the same researchers. The non-uniform patterns work against Target Row Refresh (TRR), a technique used to mitigation of earlier Row Hammer type attacks (generally tracks the number of times a row is accessed and recharges neighboring victim rows when there are signs of abuse). It is still possible to trigger Rowhammer bit flips on all DRAM devices today despite deployed mitigations on commodity off-the-shelf systems with little effort. So the memory chips were not as resistant to Row Hammer type attacks that many people thought they were. This puts further pressure on chipmakers to try to mitigate the attacks.
Blacksmith Demo – showing how easy and quick it is to find bit flips on TRR-enabled DDR4 devices
For more details read the research paper BLACKSMITH: Scalable Rowhammering in the Frequency Domain.
Sources:
DDR4 memory protections are broken wide open by new Rowhammer technique
Blacksmith
BLACKSMITH: Scalable Rowhammering in the Frequency Domain
Blacksmith: Rowhammer Fuzzer Bypasses Existing Protections
6 Comments
Tomi Engdahl says:
https://thehackernews.com/2021/11/new-blacksmith-exploit-bypasses-current.html
Tomi Engdahl says:
https://arstechnica.com/gadgets/2021/11/ddr4-memory-is-even-more-susceptible-to-rowhammer-attacks-than-anyone-thought/
jigsaw puzzle says:
Many researchers have demonstrated that repeatedly accessing specific storage locations in memory can cause bit flips – that is, bits in adjacent rows are changed from 0 to 1 and vice versa
https://jigsawpuzzle.io
Tomi Engdahl says:
BLACKSMITH: Scalable Rowhammering in the Frequency Domain
https://comsec.ethz.ch/wp-content/files/blacksmith_sp22.pdf
Blacksmith Rowhammer Fuzzer
https://github.com/comsec-group/blacksmith
This repository provides the code accompanying the paper Blacksmith: Scalable Rowhammering in the Frequency Domain that is to appear in the IEEE conference Security & Privacy (S&P) 2022.
This is the implementation of our Blacksmith Rowhammer fuzzer. This fuzzer crafts novel non-uniform Rowhammer access patterns based on the concepts of frequency, phase, and amplitude. Our evaluation on 40 DIMMs showed that it is able to bypass recent Target Row Refresh (TRR) in-DRAM mitigations effectively and as such can could trigger bit flips on all 40 tested DIMMs.
Tomi Engdahl says:
There’s a new way to flip bits in DRAM, and it works against the latest defenses
https://arstechnica.com/security/2023/10/theres-a-new-way-to-flip-bits-in-dram-and-it-works-against-the-latest-defenses/
New technique produces lots of bitflips and could one day help form an attack.
In 2015, researchers reported a surprising discovery that stoked industry-wide security concerns—an attack called RowHammer that could corrupt, modify, or steal sensitive data when a simple user-level application repeatedly accessed certain regions of DDR memory chips. In the coming years, memory chipmakers scrambled to develop defenses that prevented the attack, mainly by limiting the number of times programs could open and close the targeted chip regions in a given time.
Recently, researchers devised a new method for creating the same types of RowHammer-induced bitflips even on a newer generation of chips, known as DDR4, that have the RowHammer mitigations built into them. Known as RowPress, the new attack works not by “hammering” carefully selected regions repeatedly, but instead by leaving them open for longer periods than normal. Bitflips refer to the phenomenon of bits represented as ones change to zeros and vice versa.
Further amplifying the vulnerability of DDR4 chips to read-disturbance attacks—the generic term for inducing bitflips through abnormal accesses (i.e., activations) to memory chips—RowPress bitflips can be enhanced by combining them with RowHammer accesses. Curiously, raising the temperature of the chip also intensifies the effect.
“We demonstrate a proof of concept RowPress program that can cause bitflips in a real system that already employs protections against RowHammer,” Onur Mutlu, a professor at ETH Zürich and a co-author of a recently published paper titled RowPress: Amplifying Read Disturbance in Modern DRAM Chips, wrote in an email. “Note that this is not in itself an attack. It simply shows that bitflips are possible and plenty, which can easily form the basis of an attack. As many prior works in security have shown, once you can induce a bitflip, you can use that bitflip for various attacks.”
RowPress: Amplifying Read Disturbance in Modern DRAM Chips
https://people.inf.ethz.ch/omutlu/pub/RowPress_isca23.pdf
Memory isolation is critical for system reliability, security, and safety. Unfortunately, read disturbance can break memory isolation in modern DRAM chips. For example, RowHammer is a well-studied read-disturb phenomenon where repeatedly opening and closing (i.e., hammering) a DRAM row many times causes bitflips in physi cally nearby rows.
This paper experimentally demonstrates and analyzes another widespread read-disturb phenomenon, RowPress, in real DDR4 DRAM chips. RowPress breaks memory isolation by keeping a DRAM row open for a long period of time, which disturbs physi cally nearby rows enough to cause bitflips. We show that RowPress amplifies DRAM’s vulnerability to read-disturb attacks by signifi cantly reducing the number of row activations needed to induce a bitflip by one to two orders of magnitude under realistic conditions
Tomi Engdahl says:
This Week In Security: Flatpak Fixes, Android Malware, And SCADA Was IOT Before IOT Was Cool
https://hackaday.com/2026/04/10/this-week-in-security-flatpak-fixes-android-malware-and-scada-was-iot-before-iot-was-cool/
Rowhammer attacks have been around since 2014, and mitigations are in place in most modern systems, but the team at gddr6.fail has found ways to apply the attack to current-generation GPUs.
Rowhammer attacks attach the electrical characteristics of RAM, using manipulation of the contents of RAM to cause changes in the contents of adjacent memory cells. Bit values are just voltage levels, after all, and if a little charge leaks across from one row to the next, you can potentially pull a bit high by writing repeatedly to its physical neighbors.
https://gddr.fail/